Security Week 24: Escalating Privileges on Linux
Thursday June 10th, GitHub Security Lab researcher Kevin Backhouse published details of the vulnerability in the polkit service, which is included by default in most Linux distributions. The vulnerability allows a user with normal privileges to elevate privileges in the system to the maximum, more precisely, to create a new user with root privileges.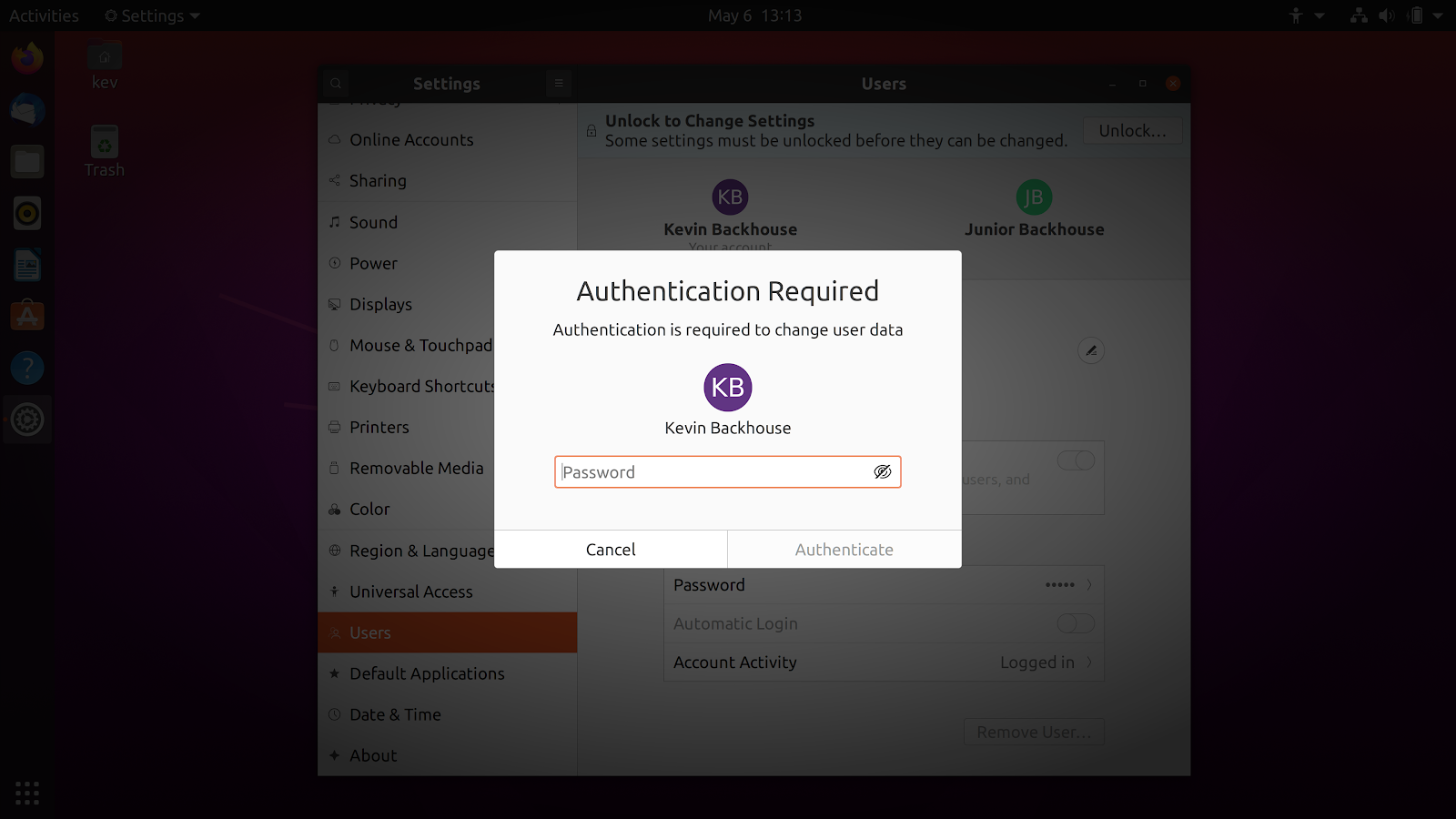
Polkit service is responsible for authorizing the user, he checks the presence of the necessary rights to execute the command, and in the graphical interface his work is usually limited to a window asking for a password. It is used by the systemd system software; polkit can also be invoked via the command line. The vulnerability is exploited through a simple set of commands. If, at a good moment, “kill” the process with a request to create a new user, an error in the polkit code will lead not only to create a new user, but also to add him to the sudo group.
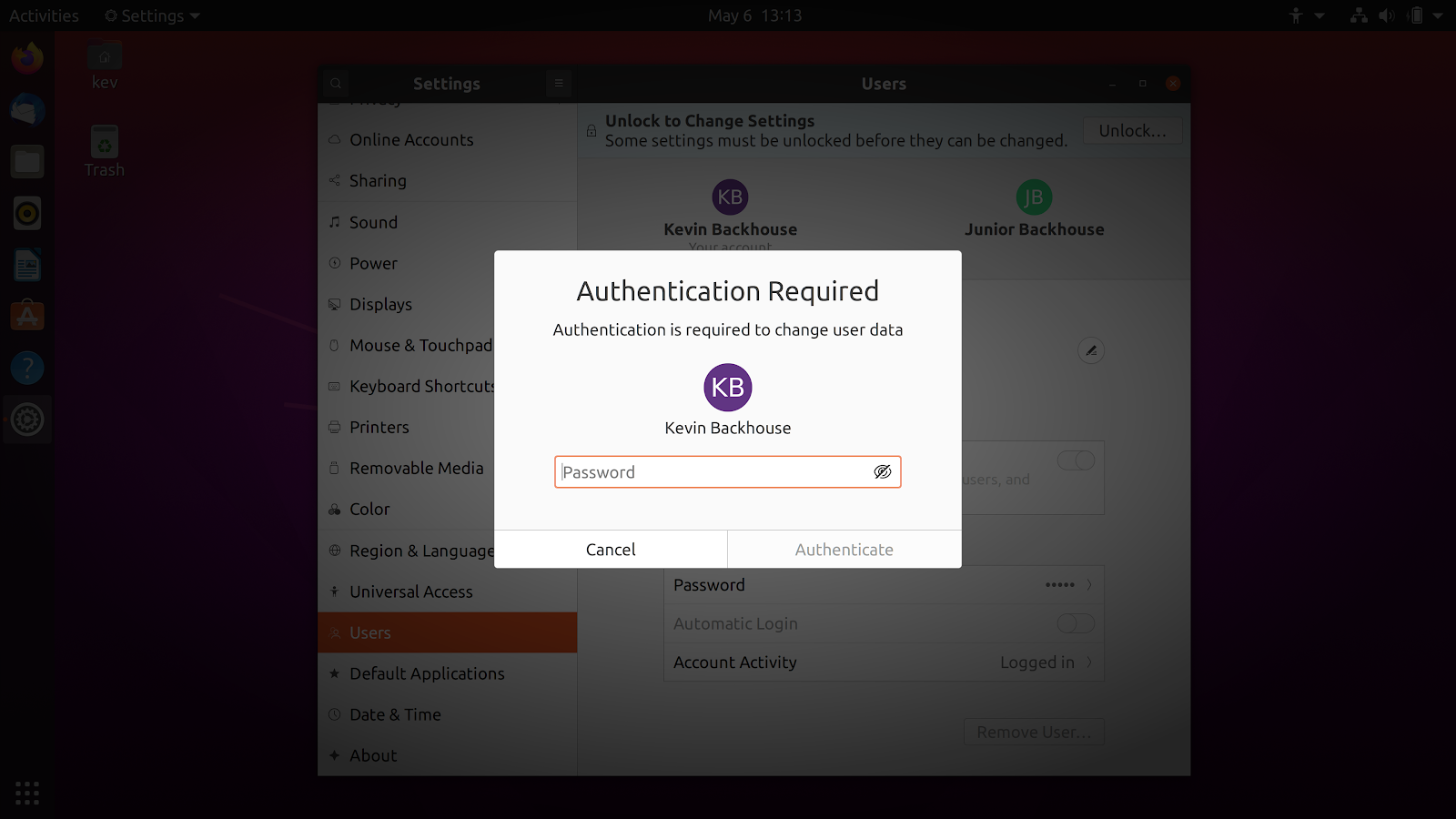
Polkit service is responsible for authorizing the user, he checks the presence of the necessary rights to execute the command, and in the graphical interface his work is usually limited to a window asking for a password. It is used by the systemd system software; polkit can also be invoked via the command line. The vulnerability is exploited through a simple set of commands. If, at a good moment, “kill” the process with a request to create a new user, an error in the polkit code will lead not only to create a new user, but also to add him to the sudo group.
Then everything is simple: we create a password for the user (we do not have the right to do this yet, but we are using the vulnerability again) and gain unlimited control over the system. The sequence of commands is described in Beckhouse’s article and shown in this video: