Security Week 12: SMB Critical Vulnerability
 Microsoft March 10 rolled out the next monthly update set covering 115 vulnerabilities in its products – from Windows 10 to the Azure cloud service. And on March 11, I had to release an extraordinary patch for a critical problem in implementing the SMB protocol in Windows 10 (news, newsletter Microsoft Description patch, discussion on Habré).
Microsoft March 10 rolled out the next monthly update set covering 115 vulnerabilities in its products – from Windows 10 to the Azure cloud service. And on March 11, I had to release an extraordinary patch for a critical problem in implementing the SMB protocol in Windows 10 (news, newsletter Microsoft Description patch, discussion on Habré).
An initial warning of a vulnerability was distributed the day before the release of the patch, and for a rather non-standard reason. Articles describing the vulnerability were mistakenly published by Cisco Talos and Fortinet, which apparently was the result of a misunderstanding between them and Microsoft in a joint research process. Publications have been removed, but as a precaution, Microsoft has issued recommendations for protecting SMB servers. There was no workaround for customers before the patch was released, which posed a certain danger, since a hole in Windows 10 (and in two versions of Windows Server) could be exploited to execute arbitrary code.
Vulnerabilities are affected by systems that use the SMB protocol version 3.1.1 – these are the Windows 10 releases of 1903 and 1909, as well as similar versions of Windows Server distributed through a special channel with regular updates once every six months. Regular installations of Windows Server, as well as earlier user versions of Windows, are not affected – obviously, it was introduced into the SMB code for file sharing recently.
Basic vulnerability description published Duo Security, based on those very remote Fortinet and Cisco Talos content. This is a buffer overflow error leading to the execution of arbitrary code on an unpatched system. An attack on the SMB server can be carried out from any client with access; To attack client software, you need to implement a script to connect to a modified server. This brief description hints that the vulnerability could be “wormable”. That is, it was used by an attacker to sequentially infect all affected systems, for example, inside the corporate perimeter.
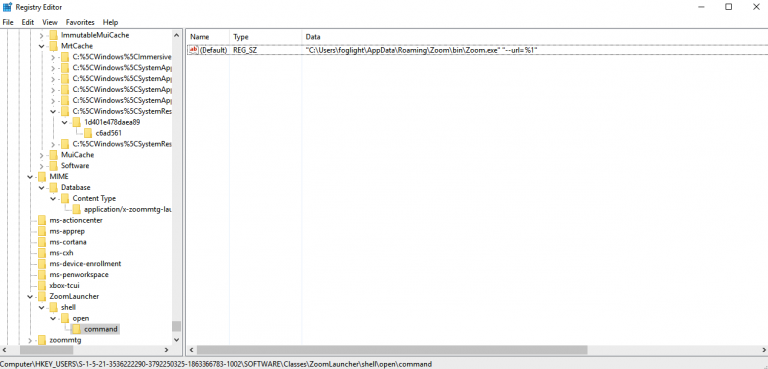
Hence Microsoft’s recommendations: restricting access via SMB, closing ports for external access. In a separate document are given settings to block port-related file sharing when the computer is connected to an untrusted network. Thus, you can reduce the risk of an attack on an employee’s computer in a common scenario of remote work from home or when using public Wi-Fi. Another initial recommendation to protect the file server — disabling data compression — indicates a possible source of the problem.
What else happened
In newer versions of Firefox 73 and ESR 68.6 closed five critical vulnerabilities and one funny. Vulnerability CVE-2020-6812 “May lead to disclosure of the real username when used on Apple devices.” More precisely, if an iPhone user also has AirPods and allows certain sites in the Firefox browser to access the camera and microphone. By default, wireless headphones in iOS are named by their real username (for example, Jane Doe’s AirPods). If you give some site access to the camera and microphone, the name of the headphone is transmitted as the name of the device. Accordingly, the owner of the site is likely to get a real username. The problem has been resolved by forcing the renaming of audio devices like XXXX AirPods just to AirPods when processing microphone requests.