Publishing house Peter. Column editor
Hello Habitants! We suggest that you familiarize yourself with brief reviews of the new products handed over to the printing house. 
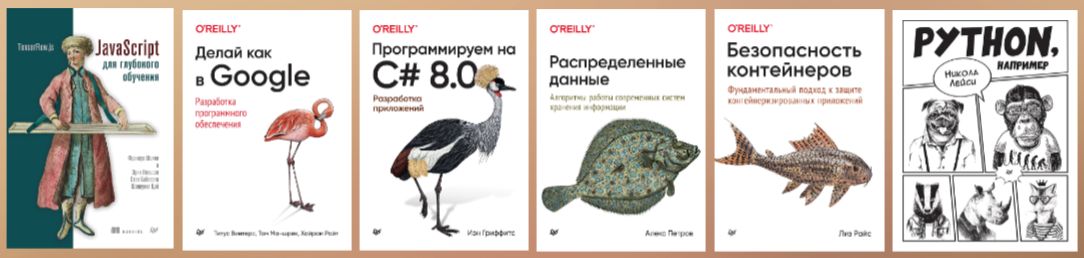
JavaScript for Deep Learning: TensorFlow.js
It’s time to learn how to use TensorFlow.js to build deep learning models that run directly in the browser!
Smart web applications have taken over the world, and TensorFlow.js allows you to implement them in the browser or back-end. This library is brilliantly portable, its models work wherever JavaScript works.
Experts from Google Brain have created a book that will help you solve real-life applied problems. You will not get bored with theory, but immediately master the basis of deep learning and get acquainted with advanced AI concepts through examples of text analysis, speech processing, pattern recognition and self-learning game AI.
In this book:
• Processing language and images in the browser.
• Fine-tuning machine learning models based on customer data.
• Create text and images using generative deep learning.
• Sample source code that you can modify and test.
Checkout pre-order…
Do it like Google. Software development
Author (s): Titus Winters, Tom Manshrek, Hiram Wright
Modern programmers must not only program efficiently, but also know good engineering practices to make the codebase stable and of high quality.
What is the difference between programming and software engineering? How can a developer manage a living codebase that evolves and responds to changing requirements throughout its existence?
Drawing on Google’s expertise, software engineers Titus Winters and Hiram Wright, along with Tom Manshreck, provide a candid and insightful analysis of how the world’s leading practitioners create and maintain software. It’s about Google’s unique engineering culture, processes and tools, and how these aspects affect development efficiency.
You will learn the fundamental principles that software companies must consider when designing, architecting, writing, and maintaining code.
Checkout pre-order…
We program in C # 8.0. Application Development
Author (s): Ian Griffiths
C # is a universal language that can do almost anything! Ian Griffiths talks about its capabilities from the point of view of a developer who is faced with the task of quickly and efficiently creating applications of any complexity.
Lots of code examples will teach you how to work with templates, LINQ, and the language’s asynchronous features. You will understand asynchronous streams, nullable reference types, pattern matches, default implementations for an interface method, ranges and indexing syntax, and more.
In this book, you:
- Learn how C # supports classes, custom types, collections, and error handling.
- You can create high-performance, memory-efficient code with the Span
and Memory types.
- Learn to query and work with object models, databases, data streams, and XML documents.
- Use multithreading to harness the full power of parallel processing.
- Learn how the features of the asynchronous language can help improve the responsiveness and scalability of applications.
Checkout pre-order…
Distributed data. Algorithms for the operation of modern information storage systems
Author (s): Alex Petrov
When it comes to choosing, using and maintaining a database, it is important to understand its internals. How do you make sense of the vast sea of distributed databases and tools available today? What are they capable of? How do they differ?
Alex Petrov introduces us to the concepts behind the internal mechanisms of modern databases and storage. To do this, he had to summarize and organize scattered information from numerous books, articles, posts, and even from several open source databases.
You will learn about the principles and concepts used in all types of DBMS, with a focus on the storage subsystem and distribution components. These algorithms are used in databases, message queues, schedulers, and other critical infrastructure software. You will understand how modern storage systems work, and this will help you choose the right software carefully and identify potential problems.
In this book, you will delve deeper into:
- Storage engines: storage classification and taxonomy, B-tree storage engines and immutable log structures.
- Storage building blocks: Organization of database files to create efficient storage using supporting structures (page caches and buffer pools).
- Distributed Systems: A step-by-step guide to connecting nodes and processes and building complex interaction schemes.
- Database Clusters: Consistency Models in Modern Databases and the Consistency of Distributed Storage Systems.
Checkout pre-order…
Container security. A fundamental approach to securing containerized applications
Author (s): Liz Rice
In many organizations, applications run in the cloud, providing scalability and resiliency through containers and coordination tools. But is the deployed system secure enough? Aimed at practitioners, this book explores the key technologies that developers and data protection professionals can use to assess security risks and select appropriate solutions.
Liz Rice researches Linux container systems. Learn what happens when you deploy containers and learn how to assess the possible security risks of the deployed system. Get started if you are using Kubernetes or Docker and know basic Linux commands.
In this book:
- Explore vectors of attacks on container deployments.
- Diving into the Linux components behind containers.
- We are taking measures to improve the safety of containers.
- Find out how configuration errors can lead to container isolation failures.
- Exploring the best practices for creating container images.
- We identify container images containing known software vulnerabilities.
- We use secure connections between containers.
- We work with security utilities to prevent attacks on the deployed system.
Checkout pre-order…
Python for example
Author (s): Nicola Lacy
This is Python, for example! Meet the fastest growing programming language today.
This easy and fun guide will help you improve your development skills step by step. No computer architectures, programming theories and other gibberish – more practice! The book contains 150 problems that will smoothly transfer the reader from learning the basics of the language to solving more complex things. The guide is suitable for anyone who is dizzy with technical jargon and lengthy explanations – the author is confident that you can learn without it.
Checkout pre-order…