WireGuard – Fast and Secure VPN in Linux Kernel
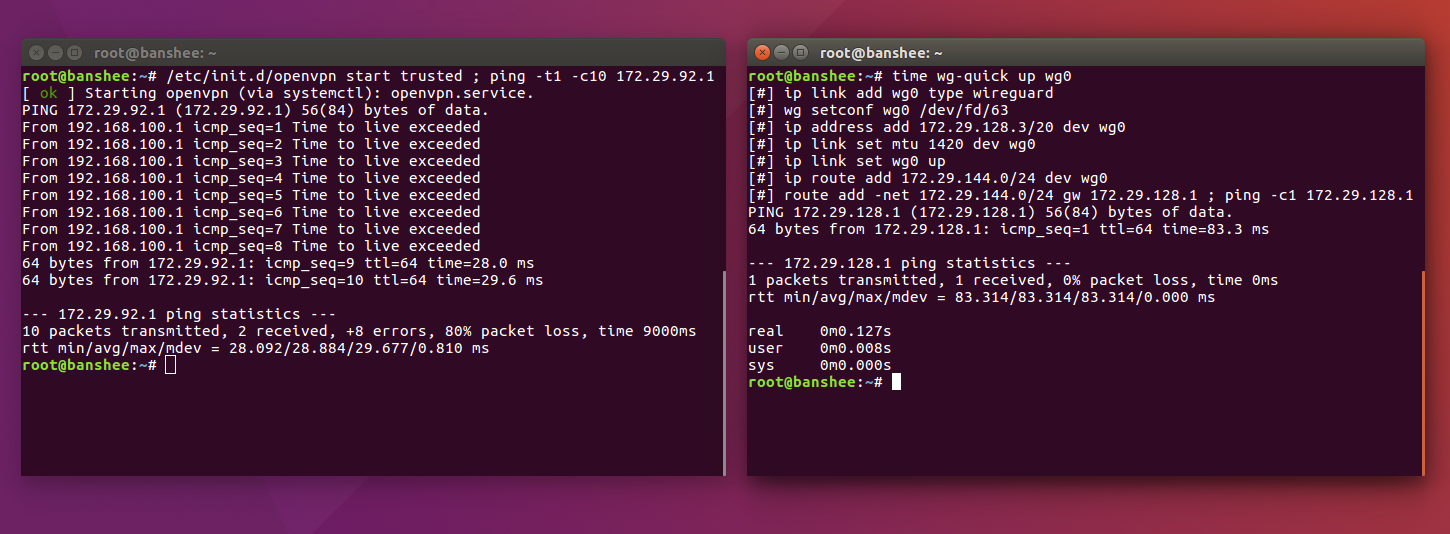
Fig. 1. OpenVPN vs WireGuard, test Ars technica
Wireguard – A free and open virtual private network protocol designed to replace IPsec and OpenVPN. In January 2020, after a year and a half of code refinement, a long-awaited event nevertheless took place – Linus Torvalds accepted VPN WireGuard in the main branch of Linux 5.6.
Very soon, this VPN will become part of the Linux kernel – the heart of an open source operating system that runs the whole world, from web servers to Android phones and cars. This is a really important event because WireGuard is designed much easier and more logical than previous VPNs. In June 2019 automated cryptographic evidence received mathematics protocol.
VPN is an important tool for security and privacy. In fact, it is an encrypted communication channel between two or more devices that allow data to be routed through a secure “tunnel”. Companies use a VPN to remotely access employees to the corporate network, and commercial VPN services offer users protection against traffic interception by directing it through remote servers. This means that your provider, government intelligence agencies or any unauthorized persons cannot see what you are doing on the Internet. Routing traffic through a remote server can also create the impression that you are accessing the Internet from another place. This allows people in countries such as China and Russia to access sites that are blocked internally.
But VPN connections are only as secure as the software itself. Security professionals have traditionally been critical of VPN software. One reason for this is that most VPN software is incredibly complex. The more complex the software, the more difficult it is to audit for security issues.
Old VPN programs are “too huge and complex, and in principle it is impossible to view and check whether they are safe or not,” is talking Jan Jonsson, CEO of the Mullvad VPN provider, which runs the built-in VPN service in the Firefox browser.
The author of WireGuard is hacker and pentester Jason A. Donenfeld. He managed to write much simpler and more concise code than in most other VPN programs. The first version of WireGuard contained less than 4,000 lines of code – compared to tens of thousands of lines in other VPN programs. This does not make WireGuard safer, but it makes troubleshooting much easier. The key mechanisms of the encryption protocol are shown in Fig. 2.

Fig. 2: (a) WireGuard protocol; (b) cryptographic computing; (c) WireGuard cookie mechanism to protect the host from DoS attacks
WireGuard clients are already released for Android, iOS, MacOS, Linux, and Windows. Cloudflare launched the Warp VPN service based on the WireGuard protocol, and several commercial VPN providers also allow users to use the WireGuard protocol, including TorGuard, IVPN, and Mullvad.
The implementation of WireGuard directly in the kernel, which directly interacts with the hardware, should further accelerate the work of the program. WireGuard will be able to encrypt and decrypt data directly from a network card, without the need to transfer traffic through the kernel and software at a higher level.
The official release of Linux 5.6 will take place in a few weeks. After that, it can be expected that the WireGuard protocol will become more widespread in various VPN services, including to protect connections between IoT devices, many of which work on Linux.
The author of the program, Jason Donenfield, made a living by breaking into computer systems (penetration tests as part of an official contract for consulting services). He originally developed WireGuard as a data exfiltration tool to covertly capture data from a victim’s computer.
In 2012, Jason moved to France and, like many VPN users, wanted to go online from an American site. But he did not trust the existing VPN software. In the end, he realized that he could use his exfiltration tool to route traffic through his parents’ computer in the USA: “I realized that many methods of hacking systems (offensive security) are actually useful for protection,” said He is in an interview with Wired magazine.
Donenfeld changed the traditional approach that VPNs and cryptographic software have used for decades. For example, other VPN systems allow users to select one of several encryption algorithms. But support for multiple encryption schemes makes the software more complex and provides more room for errors. WireGuard takes the liberty of making some decisions for the user. This makes the program not as flexible as IPsec and OpenVPN, but WireGuard is an order of magnitude simpler, which, according to proponents, reduces the likelihood of errors from both WireGuard developers and users.
A simple code audit is not the only reason WireGuard has attracted so much attention. The biggest advantage of WireGuard is that “it’s nice to use it, – is talking Thomas Ptacek, security researcher. “It’s no more difficult to configure than any of the network tools that developers are already using.”
WireGuard is on a par with the secure Signal messenger – they are part of a broad movement to create better, more convenient software based on modern cryptographic methods.
In 2019, specialists from the French Institute for Computer Research and Automation conducted WireGuard Cryptography Evaluation. They got the automated cryptographic proof of the mathematical methods underlying WireGuard, although there may still be security issues in the skin itself. Now it is being tested by Linux developers, and Donenfeld fixed several problems in anticipation of the release of the new Linux kernel 5.6 and WireGuard 1.0.

Small and Medium Business PKI Solutions from GlobalSign Certification Authority For details, contact the managers +7 (499) 678 2210, sales-ru@globalsign.com.


![[Личный опыт] Professional emigration: how Amsterdam differs from Riga and Booking.com differs from a young startup](https://prog.world/wp-content/uploads/2020/09/e460e2abb10bf9387c6ea1f292cc4197-768x576.jpg)