Telecom digest – materials about the work of providers

/ CC BY / Tim reckmann
IPv6 vs IPv4
- 5 reasons why switching to IPv6 takes so long
Registrars run out of free IPv4. In 2015, the North American ARIN pool was empty, and last year, the addresses ended at RIPE, which is responsible for the distribution of resources in Europe and Asia. The solution to the problem should be the next-generation IPv6 protocol, but its adaptation is slow – today it supports only 15% of sites. There are several reasons for this: high cost, lack of backward compatibility and technical difficulties. For example, at the end of last year, an Australian Internet service provider suspended IPv6 testing due to a bug in Cisco ASR that interferes with user authentication.
- IPv4 Addresses End – Depletion Timeline
According to Geoff Huston, APNIC chief engineer, IPv4 stocks will be empty this year. His forecast makes sense, given that each registrar has only a small pool of addresses, most of which are unused IPv4 that have returned to circulation. This is our retrospective material on how the addresses ended and what the future of external IP addressing will be. In particular, we will talk about IPv6 and NAT mechanisms.
- IPv6 Implementation – FAQ for Internet Service Providers
A kind of checklist for telecom operators who want to transfer their IT infrastructure to a new generation protocol. We examined the most common difficulties – outdated hardware, incompatibility of client equipment, as well as legislative aspects.
- IPv4 to IPv6 Migration Techniques – How They Affect IoT
It is believed that the transition to IPv6 will positively affect the security of the IoT ecosystem. The new generation protocol supports E2E encryption and offers a more robust name resolution process than IPv4. This article is a technology review from an engineer from Oxford University in which he compares several migration methods to IPv6 and evaluates their impact on the performance of IoT devices. In particular, it will be about Dual Stack, Tunneling and Network Address Translation-Protocol Translation (NAT-PT).
On the construction of networks of telecom operators
- Shot in the foot: we analyze errors in the construction of networks of telecom operators
“Bad advice” about building networks for providers based on real experience. We are talking about approaches to maintenance, architecture, monitoring and redundancy of equipment that will work like a time bomb.
- How to start your service provider
This is a step-by-step guide for those who want to become an Internet access provider over wireless networks (Wireless ISP). The material covers all important aspects: from market analysis to designing a network topology and supporting its performance. You can evaluate the effectiveness of the methods in practice in the blog of Chris Hacken – he shared a story about how he founded a network operator in Pennsylvania in 2017. He shared photos of the equipment and talked about the difficulties he encountered – channel overload and static electricity, which interfere with the work of iron. Although the instructions are aimed at the American market, several recommendations can be applied in our realities.

/ CC BY-SA / Apichart meesri
- Internet to the village – we are building a radio relay Wi-Fi network
In Russia, there are still many places where there is no Internet. The problem is gradually being solved by large providers who lay optical lines to remote villages. But for small carriers, it’s faster and cheaper to build a wireless relay Wi-Fi network. In the article, we talk about two implementation methods: point-to-point and point-to-multipoint. In the first case, the antennas “see” each other and form a radio bridge, and in the second, one base station serves several clients.
- Wi-Fi Alliance introduced Wi-Fi 6
In 2018, the Wi-Fi Alliance announced the Wi-Fi 6 specification. This article is an overview of the capabilities of the standard. It added the simultaneous support of frequencies of 2.4 and 5 GHz, as well as the OFDMA function – it allows you to transfer data to multiple clients with an average speed. At the end of 2019, the standard approved, and the first devices have already appeared on the market. According to testsThe wireless bandwidth will reach 700 Mbps.
Information Security
- How to detect Brute Force in the operator’s network
Hackers often use brute force to crack passwords and form botnets from computers and smart devices. Internet service providers can prevent this if they notice suspicious activity in time. The article talks about several triggers that help to identify this activity. For example, a large number of short sessions for one subscriber. We will also talk about the provider’s tools to prevent brute force attacks and provide statistics on the most common passwords in the world.

/ CC BY-SA / Tim reckmann
- DNS over HTTPS – security or complexity
In 2018, the Internet Engineering Council (IETF) approved DNS over HTTPS (DoH), which encrypts requests to the DNS server. This decision caused heated debate on thematic sites in the media, which have not subsided so far. Some experts are convinced that the new protocol will increase security on the Internet, the other half say that it only creates additional difficulties for system administrators. In the article, we give the views of large cloud providers, telecoms and information security companies on this issue – Mozilla, Google, FireEye and British Telecom.
- DNS-over-HTTPS and DNS-over-TLS – situation analysis
Material to continue the topic of controversy over DoH and DoT. The author parses the features of two protocols that affect the security of the network. We are talking about the DNSSEC mechanism, as well as ports 443 and 853 – how working with them affects the tasks of system administrators.
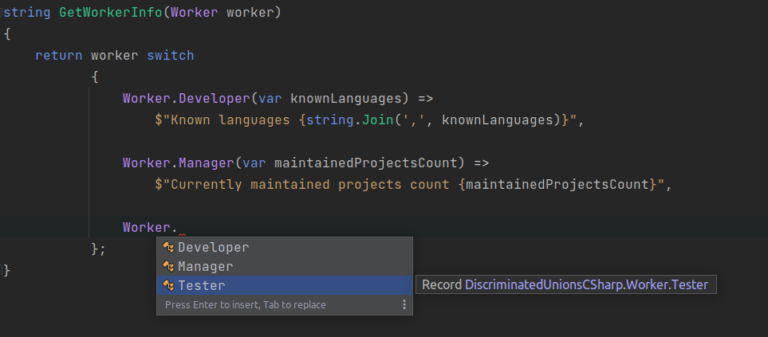
A couple of materials from our blog on Habré:
- How an enthusiast raised a Wi-Fi network under DOS
- “Stayin ‘alive, stayin’ alive”: the new protocol will increase the radius of the possible use of Wi-Fi by 60 meters
- U.S. court allows states to return network neutrality