Remote Electronic Voting: Trusted Electoral System Architecture
Materials of the cycle:
- Alexey Shcherbakov – “Lessons from electronic voting in the Moscow City Duma 2019”
- Oleg Artamonov – “Remote electronic voting: architecture of a trusted electoral system”
- Round table “Press the button: theory and practice of electronic voting”
We emphasize: the fact that there is no reason to trust the system does not mean that the results are necessarily falsified. That means they could to be falsified.
The topic of DEG has gained a second wind in recent months – in connection with coronavirus and ubiquitous karateins, while the same arguments have been preserved, in the first place, the simplicity and cheapness of such a vote. Offline work with voters is so expensive that it is expensive even for the state – and for most individual parties it is simply impossible due to the lack of resources for its organization.
Another question, purely technically, is whether it is possible to make DEG generally resistant to falsification to a degree comparable to “paper” voting.
Out of the box, classic paper voting provides us with at least:
- secrecy of voting (the gap between the authentication of the voter and the fixing of his vote);
- audit of the voters list (roll-call list of voters);
- audit of voting results (the possibility of recounting ballots);
- concealment of results until the end of voting (impossibility to determine the outcome before the end of voting).
Let’s figure out if all this can be implemented in DEG (answer for the impatient: yes).
Secret of voting
In classic old-mode voting, the secrecy of the vote is secured by a physical gap between the two places – the place where the voter certifies his right to vote and the place where he casts his vote. In the first place – this is the table of the election commission of the precinct – the voter is identified by his passport and he is given an anonymous bulletin. In second place – the ballot box – the fact of having a ballot is a confirmation of the right to vote, the identity of the voter is already unimportant and, in fact, unknown.
In the vast majority of DEG systems implemented by both the authorities and the opposition, both in Russia and abroad, there is no such gap: authentication and voting take place on the same server controlled by the same people. Which, of course, may have their own political interests and, accordingly, be potentially unscrupulous at hand.
At the same time, there is no fundamental need to build DEG in this way – except, of course, the logic “it’s easier for us”.
For the past three decades, cryptography experts have been developing and analyzing the so-called “voting protocols”, which make it possible to realize the secret of voting “in hardware”.
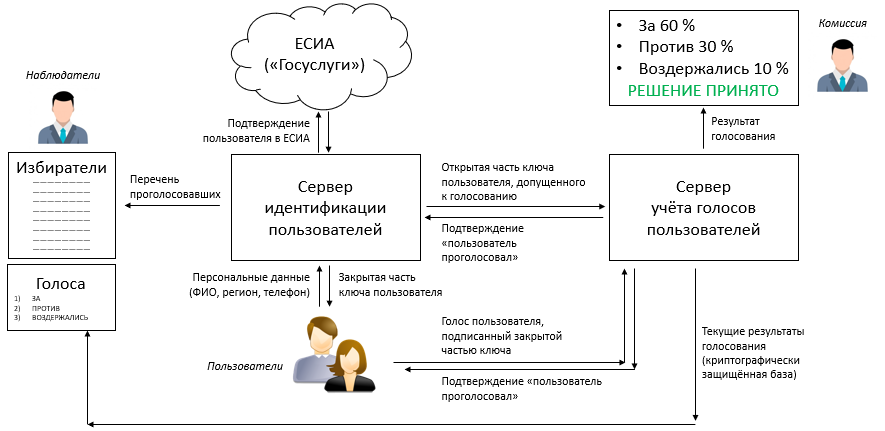
The only critical implementation requirement is the presence of two servers under the control of forces independent from each other (for example, two fractions or two committees within the party, if we are talking about the internal party system).
User authentication server checks if the given user can vote, and if so, generates two halves of the key. One half goes to vote server, the second is transmitted to the voter to the device from which he is voting.
At the moment of casting a vote, this vote is signed by the voter’s key and sent to the voting server, which verifies the keys and takes into account the vote. The fact that the voter has his half of the key is a confirmation of his right to vote; the voter server does not know and cannot know the identity of the voter.
In the event that an open vote is held, after the vote is received, the vote server sends information about it to the user authentication server, which compares the key with the name and surname and publishes this information in the list of authenticated voters.
In the case of secret voting, the vote server only confirms the fact of the completed vote to the authentication server.
An important nuance in the implementation of such a scheme is to take into account the possibility of attacks based on indirect data, which may include the fingerprint of the user’s device, the user’s IP address and voting time. While ensuring the independence of the two servers used here, only the voting time is critical – you can compare the user authentication time and the time the voice was added to the database; therefore, the interaction scheme between servers and users should provide for the destruction of this connection in an explicit form, at least by adding a random delay between authentication and sending voice from the device used by the user to vote.
The rest is a scheme with two independent servers – and only it! – allows you to realize the secret of voting in electronic form.
Schemes that use a single server, trusted in this context cannot be considered by definition; all statements by their authors about the lack of registration of voter names in conjunction with their votes are based solely on trust in the cleanliness and accuracy of these authors (and we all remember that in the IT industry there are thousands of examples when the author of the service did not mean anything bad, just forgot to turn off debugging in the release build).
A correctly implemented scheme with independent servers ensures the secret of voting always if the owners of both servers have not consciously taken measures to eliminate it.
User authentication
This is the easiest part of the system. Depending on the purpose and importance of voting, authentication can be carried out:
- A couple login-password or PIN-code via SMS (for example, opinion polls or solving local issues of the city economy)
- By user’s membership card number, including an electronic NFC / RFID-based membership card (for example, ongoing intra-party voting)
- Authentication in the ESIA (intra-party primaries, non-party votes, including national elections and referenda)
(ESIA – Unified Identification and Authentication System – this is an authorization system in State Services; parties have recently been allowed to use it for primaries and collection of signatures)
Note that the biometric sensors of smartphones (eyeprint sensor, iris, etc.) cannot be used for authentication in electoral systems, because they do not give out the actual biometric data, but only confirm that this person is the owner of this smartphone. The owner of five smartphones, respectively, will be able to authenticate five times. These sensors can only be used to confirm access to the application used for voting, so that an outsider who has gained access to the smartphone does not vote for its owner.
The use of biometric data for authentication in the voting system is potentially possible, but only if they are voluntarily provided by users and processed by the user authentication server, for example, based on a photograph of a person.
Audit of the voting process
One of the ways to falsify the voting results is by stuffing “extra” ballots and the so-called “carousels”.
The influence of external forces in this scheme can be excluded by elaboration of the user authentication system.
However, even with a very high reliability of the user authentication system authentication server owners can start generating “virtuals”by giving them the keys and sending them to the vote server to vote for the item that is necessary for the owners of these servers.
There are several ways to prevent this:
- unloading from the user authentication server a roll-call list of registered and voted voters, similar to paper lists of the election commission (CI), to the devices of observers and members of the CI;
- analysis of anomalies in user behavior from the server for counting votes (a large number of users from devices of the same type, identical IP addresses, abnormal distribution of users by voting time);
- lack of opportunity for observers or owners of the authentication server to find out the current distribution of votes before the end of voting.
Here we are confronted with the concept of “observer” for the first time – observers are also needed in remote voting, and they are needed for the same purpose as in paper voting. However, in this case, they do not control what is happening internally, but by uploading data to their devices from authentication and vote control servers.
Audit of voting results
The most important role of observers in the audit of voting results. It’s obvious that vote server owners can potentially just swap numbers before publishing them.
In order to prevent this, the current database of votes is regularly replicated to observer devices throughout the voting process (if you wish, you can just screw the blockchain here – but in general, not necessarily). To prevent leakage of results before the end of voting, the base is cryptographically protected.
At the end of voting and the publication of its results, the key to the database is sent to observers, so that they can independently calculate the result of voting and compare it with the published one – this will make it impossible to substitute the result.
In addition, observers can compare the number of votes registered by the vote server with the number of voters registered by the authentication server to exclude the option of throwing anonymous votes by the owners of the vote server (especially since they are potentially the only people who can monitor the voting results in real time , and therefore they can gently toss the votes in the right direction so that it is not noticeable).
In the same system, the task of preventing substitution of votes of real users – it is possible to implement the so-called audited voting system in which the user can, using an individual cryptographic key, check for whom his vote was counted, without revealing his identity and not having the opportunity to check the votes of other voters. We emphasize that in many articles such an audit exhausts the possibilities of audit – this is not true, because personal verification does not exclude the possibility of throwing in “dead souls” or substituting the final results.
Pressure Voting
A typical problem of remote and in-person voting is voting under pressure – in a situation where the head (for example, the director of an enterprise) directs employees to vote for a particular candidate by reporting photos of ballots.
Interestingly, in the case of remote voting, this threat can be leveled ability to change voice throughout the course of the vote. That is, using the key given to him, the voter can vote several times – and only the last vote cast will be taken into account, which will allow the boss to demonstrate the “correct” vote, and then vote for the really desired candidate.
In addition, post-factum detection of mass re-votes (database captures all votes, the last cast is taken into account when counting) may indicate the presence of a clear problem and a reason to start an investigation.
Conclusion
Thus, contrary to the statements of some experts, politicians and political scientists, the construction of a trusted and reliable system of remote electronic voting perhaps.
Such a system will provide a level of protection against fraud not lower, and in some cases higher than the classic face-to-face secret ballot, while significantly reducing the complexity and cost of organizing the will of citizens (residents of a country, city, members of political parties and public organizations, etc.). Most importantly, trust in the system is provided to a large extent by technological solutions, and not trust in its operators.
Due to the technological feasibility of solving the majority of possible problems for ordinary voters, the reliability and non-falsifiability of the system can be confirmed by the open opinion of experts, including third-party and independent ones, which users will not have any reason for mistrust.
The distributed nature of the system (the independent operation of two servers, observer devices and user devices) provides protection against such primitive and typical tricks as code spoofing or the launch of third-party applications that modify the system’s work, after being tested by experts – attempts to intervene in only one of the system components can disrupt its operation, but they cannot imperceptibly for the operators of other components of the system falsify data.
With the modular construction of the system, it will allow voting with different authentication methods, secret and open, with a different level of trust – depending on the issues being resolved.
P.S. Whether such systems will be put into practice by anyone is an open question. But there is a technological possibility of their development, implementation and use.
The author of the text is Oleg Artamonov (olartamonov), head of the scientific and technical examination service of the Direct Democracy Party.
Additional materials:
- Oleg Artamonov, report “Problems and prospects of electronic voting“, AnalogBytes Conference 2020, March 5, 2020
- Alexey Shcherbakov, report “Electronic voting lessons at the Moscow City Duma 2019“, AnalogBytes Conference 2020, March 5, 2020
- Bruce Schneier, “Applied Cryptography”, Chapter 6“ Esoteric Protocols ”
- Wikipedia, “Secret Voting Protocols“
- Wikipedia, “End-to-end auditable voting systems“
P.S. Tomorrow will be on the air: while Moscow’s DIT promises everything, we are already gathering lawyers, pirates, political strategists, mathematicians and hackers from Habr at the same table.