nmap scripts
Hello, Khabrovites. We are sharing with you the author’s article, which was prepared by Alexander Kolesnikov.
Also within the professional course “Network engineer” will take place soon open webinar on “NAT is not a Firewall”. Participants of the webinar, together with an expert, will consider what NAT is and why NAT! = Firewall, as well as analyze different types of configurations for different situations.
Networking is a rather complex process, and sometimes, to understand how it works, you have to use abstractions and additional tools that allow you to get information about this interaction. This article will tell you how to write scripts for the nmap tool and what they consist of.
Scripting language and main features
The official repository is hosted on the svn system, but for convenience we will use a mirror on github… Even if you don’t delve into the project code, you can easily see that the project uses the language Lua… It is a programming language that, as the authors assure, can work very flexibly with data structures. It also supports a wide variety of programming paradigms. You can get acquainted with the basic constructions of syntax here…
The nmap tool uses the Lua language because of its simplicity and lightness. Initially, this language was added so that you can quickly and easily increase the functionality of nmap. There are a large number of network protocols, so standard communication over IP, UDP, TCP and ICMP may not be enough.
So nmap contains a Lua interpreter. The programming language interpreter is integrated into nmap and interacts with it through a framework called the Nmap Scripting Engine. NSE can run scripts in parallel and work with I / O interfaces, and also provides an error handling system. All scripts that can be written to extend the work of nmap are divided into separate tasks… There are 14 of them in total, the most interesting, according to the author, can be found below:
auth – scripts that are aimed at collecting authentication data;
discovery – scripts that collect information from root entities;
external – scripts that can use third-party services to provide information;
vuln – scripts that check the service for a known vulnerability are used only for checking;
intrusive – scripts that can harm the system under investigation.
As part of our article, we will create a script for the discovery category.
Writing a script
No matter how simple a programming language is, but to really quickly and efficiently write in it, you need to use an IDE. Especially if it is a programming language that has an API through which it can communicate with the outside world. To write NSE scripts, we will use Halcyon IDE… The IDE requires an installed JRE, it looks like this when launched:

The IDE allows you to study ready-made scripts, view libraries that are available for writing new scripts, as well as functionality for debugging and running scripts in nmap.
To start writing a script, we need to understand exactly how the script is called and what parameters it can use to parse data from the network. The basic script can use the information that nmap received from the host scan:
host – an object that contains a large amount of information about the host (ip, OS version);
port – an object that contains information on the port (protocol, number, version).
In addition to the listed data, from the script you can interact with the network subsystem as if we were just writing applications to work over the network. That is, you can create a socket and use it to send and receive information. In addition, scripts can use additional parameters that are listed for the script on the command line.
Any script template has the following template:
portrule = function( host, port )
return true
end
action = function(host, port)
endportrule is a rule that is used to determine if a script should be run. Allows to set a specific port for scanning. You can also limit by host value: for this you need to change portrule to hostrule. The function returns true or false depending on whether the port or host is the same or not.
action – the main script function, fires only if the rule part returns true. May return a string or nil (empty).
Let’s test the script outside the IDE, start a listener on port 7878:
sudo nc -lvvp 7878Let’s run the spript:
sudo nmap -n --script=testScript.nse 127.0.0.1 -p 7878The result of the script:
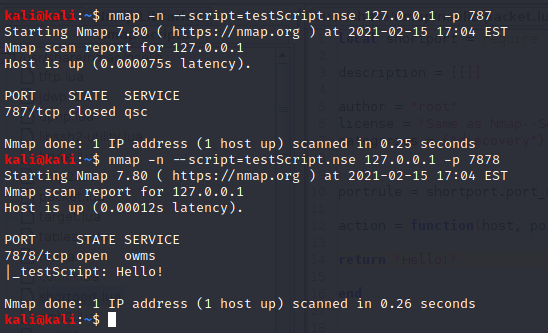
The screenshot shows an example of launching on any port that differs from what we indicated in the portrule section. And vice versa – the same port that should be processed.
Result
A script that can write notifications for a given port is a fairly simple example, but it is he who demonstrates the main elements of the script for nmap. The reader is invited to independently implement the functionality for working with the http protocol and obtaining information about the server.
Learn more about the course “Network engineer”.
Watch an open webinar on the topic “NAT is not a Firewall”.