How InTrust Can Help Reduce RDP Login Failures
Anyone who has tried to run a virtual machine in the cloud is well aware that the standard RDP port, if left open, will be attacked almost immediately by waves of brute force attacks from various IP addresses around the world.
In this article I will show you how in InTrust you can configure an automatic response to brute-force password by adding a new rule to the firewall. InTrust is a CLM platform for collecting, analyzing and storing unstructured data, which already has hundreds of predefined responses to various types of attacks.
In Quest InTrust, you can configure the response when the rule is triggered. InTrust receives a message from the log collector about an unsuccessful authorization attempt on a workstation or server. To configure the addition of new IP addresses to the firewall, you need to copy the existing specialized rule for detecting multiple failed authorizations and open its copy for editing:
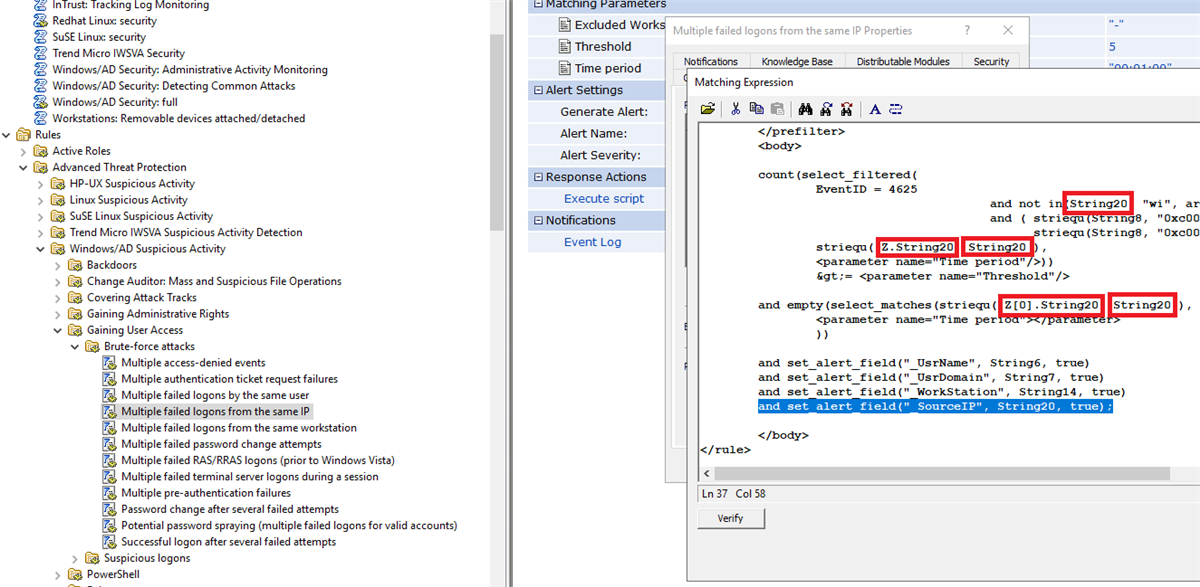
Events in Windows logs use the so called InsertionString. Look at the matches for event ID 4625 (this is an unsuccessful logon to the system) and you will see that the fields of interest to us are stored in InsertionString14 (Workstation Name) and InsertionString20 (Source Network Address), When attacking from the Internet, the field with the Workstation Name will most likely be empty, so it is important to this place substitute the value from Source Network Address.
An account failed to log on.
Subject:
Security ID: S-1-5-21-1135140816-2109348461-2107143693-500
Account Name: ALebovsky
Account Domain: LOGISTICS
Logon ID: 0x2a88a
Logon Type: 2
Account For Which Logon Failed:
Security ID: S-1-0-0
Account Name: Paul
Account Domain: LOGISTICS
Failure Information:
Failure Reason: Account locked out.
Status: 0xc0000234
Sub Status: 0x0
Process Information:
Caller Process ID: 0x3f8
Caller Process Name: C:WindowsSystem32svchost.exe
Network Information:
Workstation Name: DCC1
Source Network Address: ::1
Source Port: 0
Detailed Authentication Information:
Logon Process: seclogo
Authentication Package: Negotiate
Transited Services: -
Package Name (NTLM only): -
Key Length: 0
This event is generated when a logon request fails. It is generated on the computer where access was attempted.
The Subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe.
The Logon Type field indicates the kind of logon that was requested. The most common types are 2 (interactive) and 3 (network).
The Process Information fields indicate which account and process on the system requested the logon.
The Network Information fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases.
The authentication information fields provide detailed information about this specific logon request.
- Transited services indicate which intermediate services have participated in this logon request.
- Package name indicates which sub-protocol was used among the NTLM protocols.
- Key length indicates the length of the generated session key. This will be 0 if no session key was requested.
Additionally, add the Source Network Address value to the event text.

Then you need to add a script that will block the IP address in Windows Firewall. Below is an example that you can use for this.
param(
[Parameter(Mandatory = $true)]
[ValidateNotNullOrEmpty()]
[string]
$SourceAddress
)
$SourceAddress = $SourceAddress.Trim()
$ErrorActionPreference="Stop"
$ruleName="Quest-InTrust-Block-Failed-Logons"
$ruleDisplayName="Quest InTrust: Blocks IP addresses from failed logons"
function Get-BlockedIps {
(Get-NetFirewallRule -Name $ruleName -ErrorAction SilentlyContinue | get-netfirewalladdressfilter).RemoteAddress
}
$blockedIps = Get-BlockedIps
$allIps = [array]$SourceAddress + [array]$blockedIps | Select-Object -Unique | Sort-Object
if (Get-NetFirewallRule -Name $ruleName -ErrorAction SilentlyContinue) {
Set-NetFirewallRule -Name $ruleName -RemoteAddress $allIps
} else {
New-NetFirewallRule -Name $ruleName -DisplayName $ruleDisplayName -Direction Inbound -Action Block -RemoteAddress $allIps
}
Now you can change the rule name and description to avoid confusion later.

Now you need to add this script as a response to the rule, enable the rule, and ensure that the corresponding rule is enabled in the real-time monitoring policy. The agent must have the ability to run a response script enabled and the correct parameter must be specified.

After completing the settings, the number of failed authorizations decreased by 80%. Profit? What another!

Sometimes a small increase occurs again, but this is due to the emergence of new sources of attacks. Then everything starts to decline again.
In a week of operation, 66 IP addresses were added to the firewall rule.

Below is a table with 10 common usernames that were used for login attempts.
| Username | amount | In percents |
| administrator | 1220235 | 40.78 |
| admin | 672109 | 22.46 |
| user | 219870 | 7.35 |
| contoso | 126088 | 4.21 |
| contoso.com | 73048 | 2.44 |
| administrador | 55319 | 1.85 |
| server | 39403 | 1.32 |
| sgazlabdc01.contoso.com | 32177 | 1.08 |
| administrateur | 32377 | 1.08 |
| sgazlabdc01 | 31259 | 1.04 |
Tell us in the comments how your response to information security threats is structured. What system are you using, how convenient is it.
If you are interested in seeing InTrust in action, leave a request in the feedback form on our website or write to me in a personal.
Read our other articles on information security:
Identifying an ransomware attack, gaining access to a domain controller and trying to resist these attacks
What can be useful from the logs of a Windows workstation (popular article)
Tracking the life cycle of users without pliers and tape
Who did it? We automate information security audit
How to reduce the cost of ownership of a SIEM system and why you need Central Log Management (CLM)





