Hardware anti-skimmer. Black box protecting ATMs
Greetings to all!
I think the vast majority of people sitting here are familiar with such devices for stealing bank card data as skimmers. They were actively fought against (in some places successfully, but in others not so much), and with the spread of contactless cards they quietly and imperceptibly became history.
Many people have probably heard about special, cleverly shaped covers for card readers, designed to protect the device from the installation of foreign equipment. But everything was not limited to protective plastic parts; there were much more interesting devices, a couple of which fell into my hands.
So, in today’s article we’ll talk about such a little-known type of ATM protection among ordinary people as active anti-skimmers. Along the way, we’ll try to launch the devices I have and find out how they work. As usual, there will be a lot of interesting things.
❯ The point is this
In the era of magnetic cards, this situation was quite common – you withdraw money from an ATM in the gateway, everything goes fine, only then it suddenly turns out that there are no funds on the card. I didn’t find this carding method in our city, but in larger and more visited places such devices were actually installed. Alas, this time the reality was not so different from what was told in thematic publications – a simple pair of overlays on the reader and keyboard made it possible to steal data from everyone who used the ATM. They actively fought with these things, installing special plastic devices that prevented the installation of anything else. But, as it turned out, everything is not so simple; in fact, there were much more interesting solutions. I don’t see any point in talking about the skimmers themselves, almost everything
has already been said before me
. Today we’ll talk about how we protected ourselves from them.
❯ What else was installed to protect against such devices?

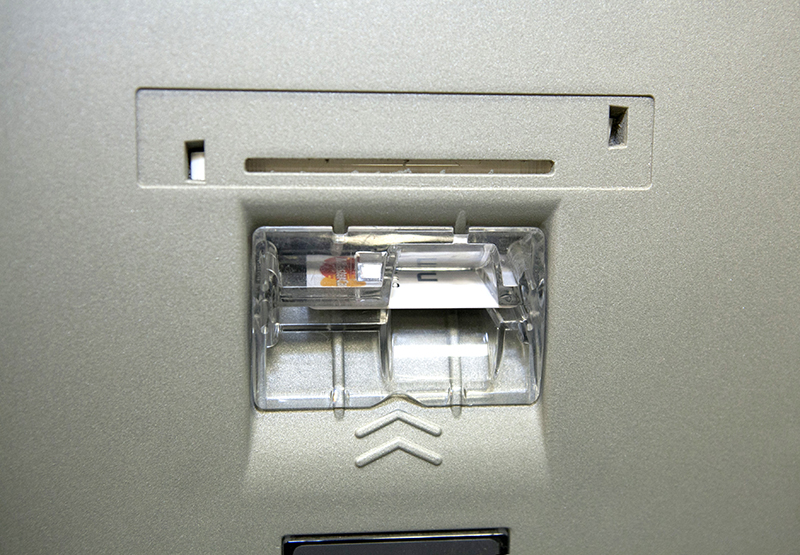
The simplest option was ordinary plastic pads. This thing made it much more difficult to install third-party equipment on the reader. And even if it didn’t make it difficult, the “mined” ATM was easily visible even to the average person.
But there is a problem – with the help of a flat screwdriver, the plastic thing could easily be torn off (after which you could insert your electronics into it and screw it onto the ATM), the transparency of many of these parts did not help much. The solution was simple – to ensure control of the integrity of this node. The cable has a snake track like in a POS terminal, and now when you tear off or dig a hole in this part, either the card reader is turned off or an alarm is triggered.

And finally, the most interesting option is hardware anti-skimmers. These devices allow you to either detect malicious devices or interfere with their operation. We'll talk about them today.
❯ What kind of devices are these?
According to their operating principle, they are much more complex than simple nozzles. Such devices were produced by several companies, but their operating principle is approximately the same.
In general, for some reason there are few mentions about the design and operation of these things; they only talk about some unique patented technologies without a detailed description of how it works.
Hardware anti-skimmers are divided into two categories – those that detect the installation of such devices (after which the ATM is usually blocked) or those that suppress their operation (while the ATM can be safely used). The latter usually have the functionality of the former, reporting suspicious activity to the bank.
A typical device of this type consists of an antenna that emits interference that interferes with the operation of the skimmer's magnetic head, volume sensors to monitor the presence of something foreign near the card reader, and limit switches to control card rolling.
❯ Equipment overview
It so happened that two such devices fell into my hands, one from the Russian company Answer Pro, the other from the Dutch TMD (not to be confused with an intercom key duplicator).

And here is the first device. A small blue box with a screen and two LEDs.

The second part of the TMD is another module that connects to the main unit with a cable with three wires.

The second device is the Russian Cerberus. It looks more modest: there are only connectors on the case and nothing else. However, I managed to find software for the second one, so most of the attention today will be paid to it.
❯ TMD
First in line will be a device from TMD Security.

In the field of ATM security equipment, this is a fairly serious company, which also produces those legendary ink cassettes, anti-explosion protection equipment and other cool equipment, which includes those same anti-skimmers.

But let's move on to our device. I don't have any pinouts for it, so in order to get it to work I had to take it apart. Inside, everything is as expected – a display (8*2, HD44780), a couple of relays, LEDs, a buzzer, a reset button, an RTC battery.

Let's remove the screen. Below it are three PIC microcontrollers. Power was found quite quickly – the first and second contacts of the rightmost connector.
We supply 24 volts, and the device starts.

But, alas, after initializing the sensors, it gives an error. I don’t have the slightest idea how these sensors work (and they are digital), just as there is no software for configuration (which is much more serious), so nothing can be done about it.
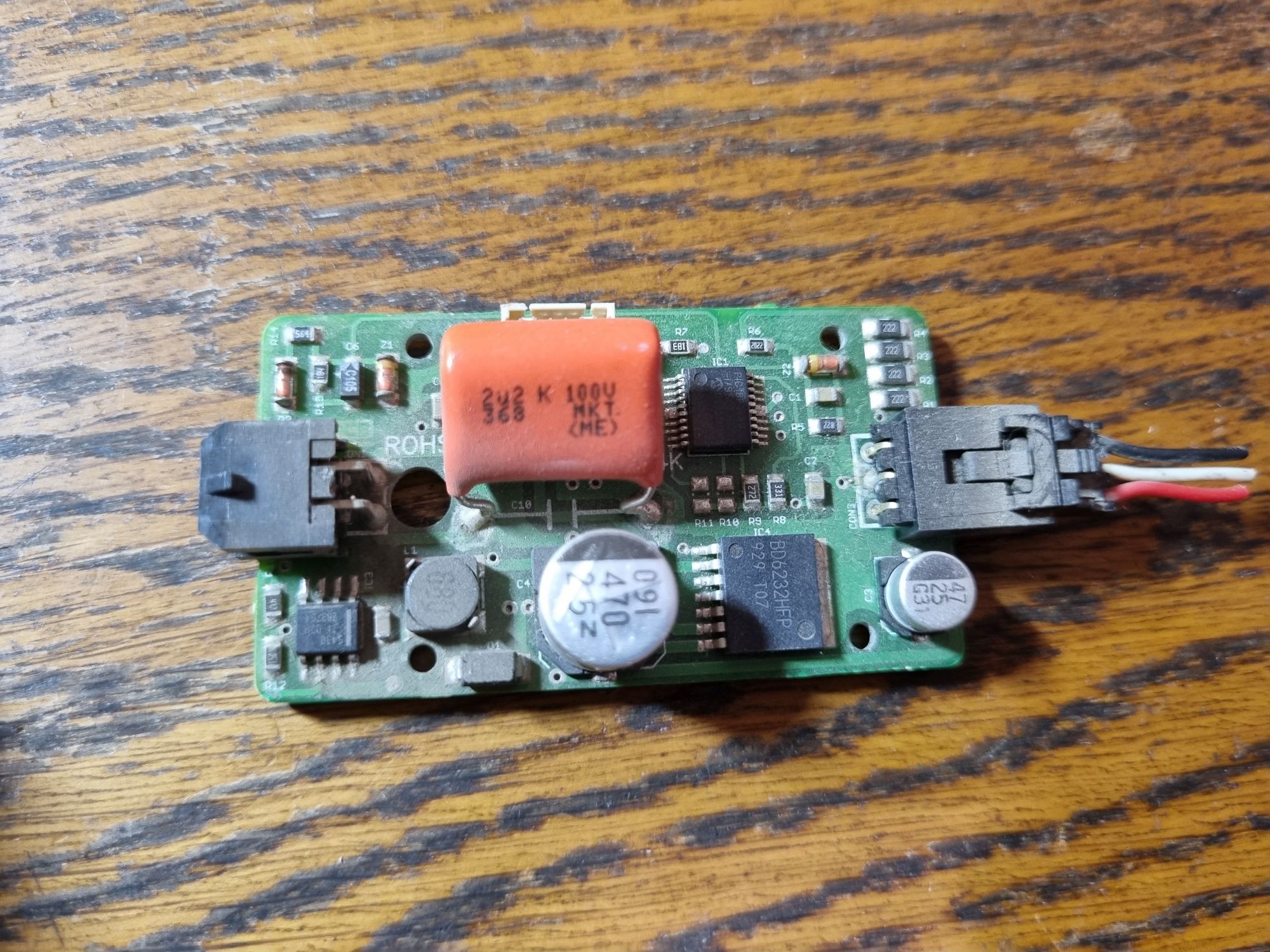
And here is the filling of the small box. This is the same jammer. There is another small PIC on the board, as well as a BD6232HFP chip – a powerful H-bridge. Generally, it is used as a motor driver, but in this case it controls a coil connected to the second connector on the board. When the device is operating, it emits a magnetic field that interferes with the operation of the skimmer's magnetic head.
❯ Cerber
Let's move on to the second device. This time it is a product from a Russian company. Her website
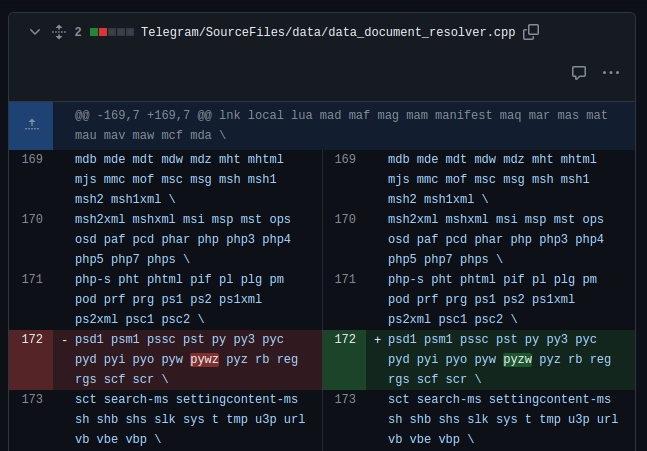
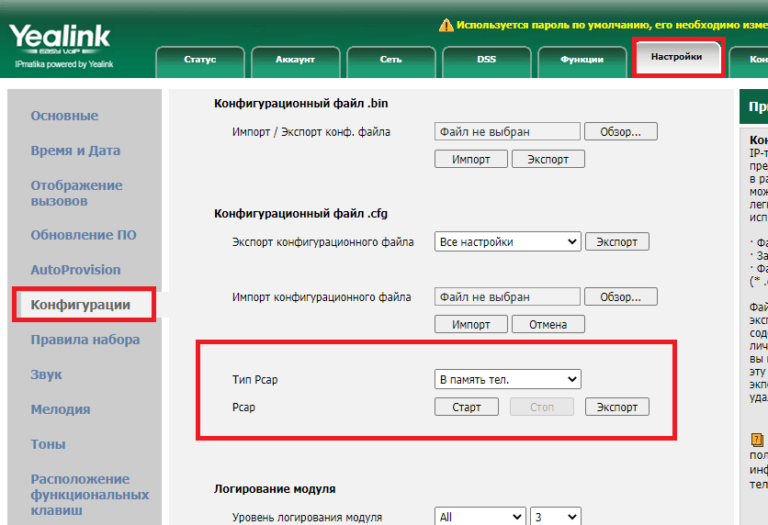
so you can immediately download drivers and software.

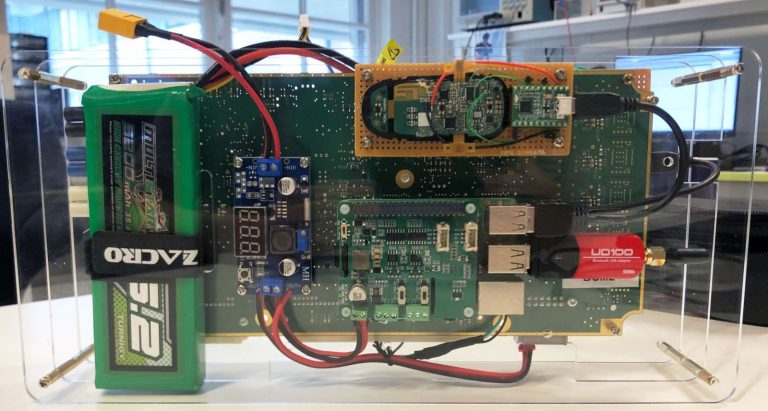
And here are the insides of the device. The power elements of the power supply circuits of the device, card reader and antenna, STM32 microcontroller, and power-off relay are clearly visible. The device is connected to the gap in the power cable of the card reader and, if necessary, can disconnect it. The same antenna is connected to the second power connector, generating interference. Three more connectors – a limit switch, a receiving antenna and a capacitive sensor. The box is connected to the computer via a USB-UART CP2102 bridge.

This is what that same reel looks like when installed on an ATM. In appearance, it is very similar to a demagnetization loop, which can be found in old TVs and monitors.

Let's launch. The relay clicks and the error LED lights up. A good start.
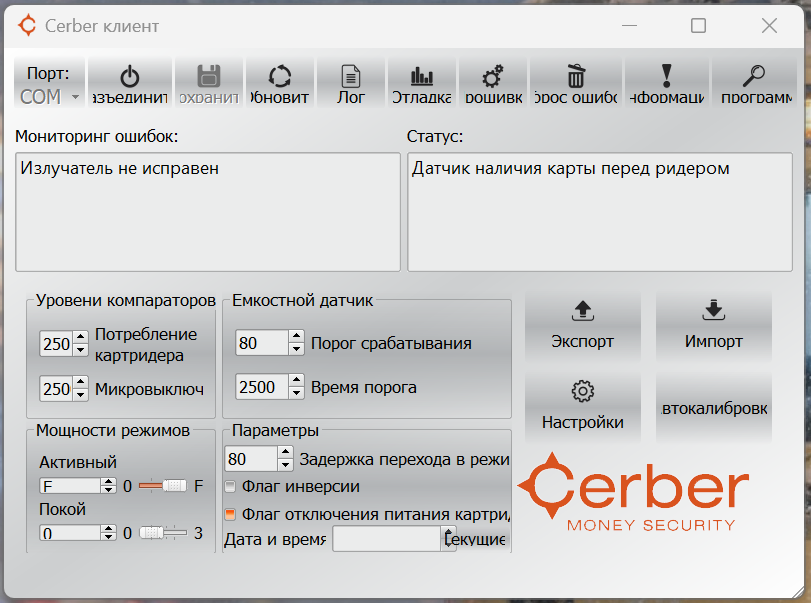
Now it's the software's turn. We launch the standard software and see in the list of errors a break in the same induction loop. I don’t have a standard coil, so instead I just connected a powerful resistor. The field created by the coil is quite powerful; with its resistance of ten ohms (as stated in the documentation), a current of about four amperes flows in it.

After that, all three LEDs, as expected, turned green.

Judging by the log, the device was last launched in 2017.

The most interesting point is debugging. Here you can view data from sensors in real time. For example, I connected a 36-volt incandescent lamp and a toggle switch to the card reader's power connector. When it was turned on and off, the values on the graph also changed.

The radiation sensor is simply an antenna in the form of a loop.

By the way, if you place the emitter next to the control unit, it will begin to react to its own interference, peaks will appear first, and then the graph will rapidly creep up.

There is obviously nothing interesting with the end switch.

The most interesting thing is the capacitive sensor, which is connected to the unit with as many as six wires. Unfortunately, I don’t have the sensor itself, and if it’s missing, the reading doesn’t work…

This is what this part looks like when installed. It allows you to monitor the presence of something foreign near the card reader slot.
❯ How does this all work?
Well, let's move on to the most interesting part – an analysis of how it all works.

Here is a typical magnetic card drive from an ATM. This particular one is NCR IMCRW, but in other models (Wincor, Diebold) these things are absolutely identical in design.
In general, I have several such devices, so perhaps someday I will tell you more about them.
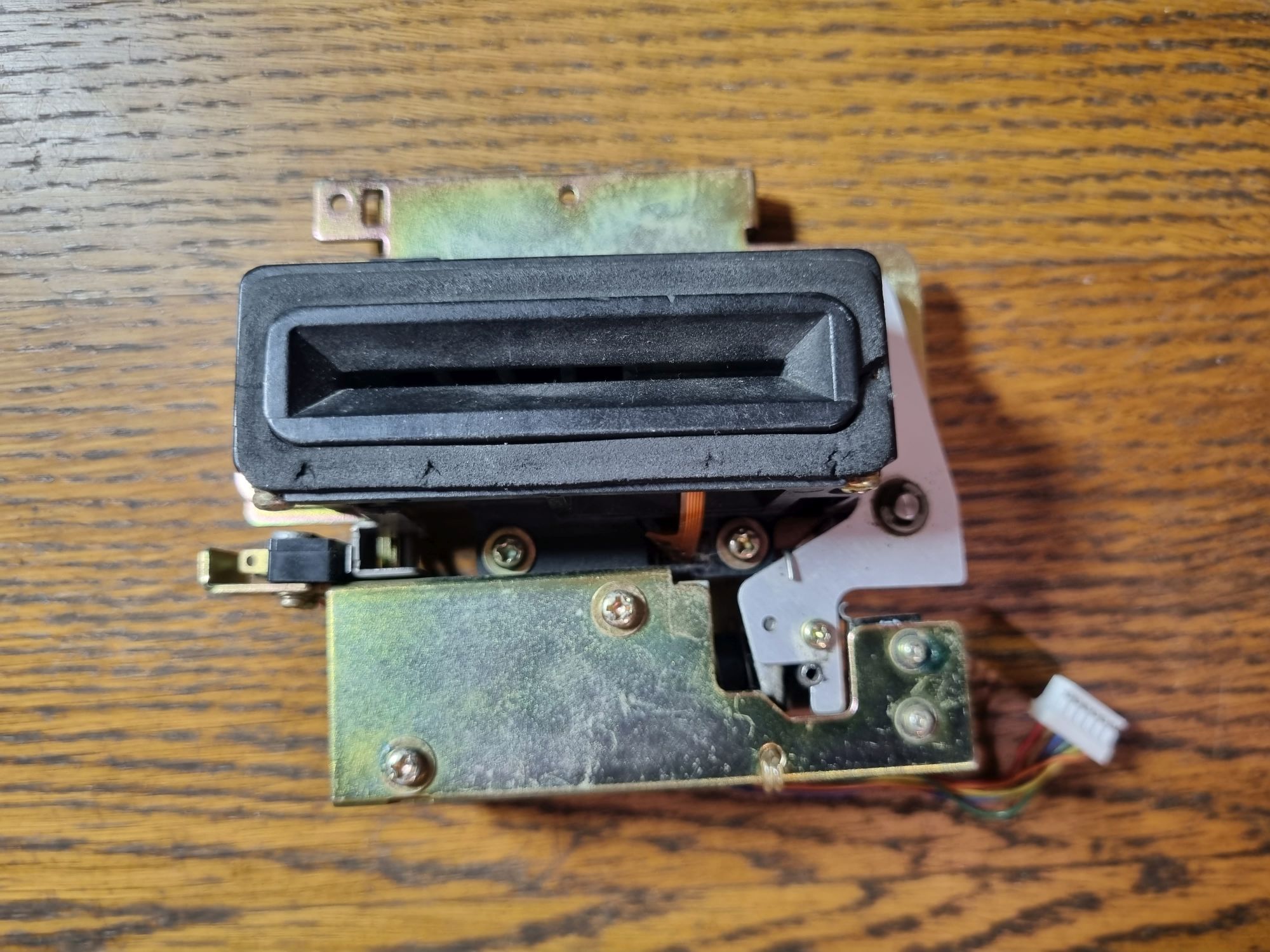
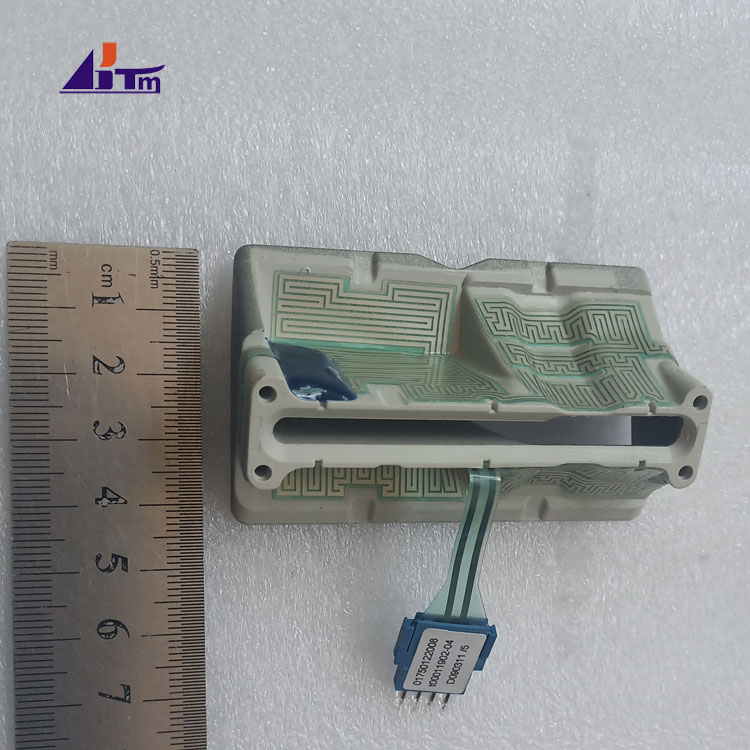
But now we are only interested in him muzzle receiving slot. For example, here is a module from the NCR MCRW card reader (not to be confused with the newer IMCRW).

The block itself came to me burnt out (they tried to start it and supplied 24 V to the 5 V bus), and I disassembled it for the sake of mechanical parts, leaving a part of the swallowing mechanism as a souvenir.
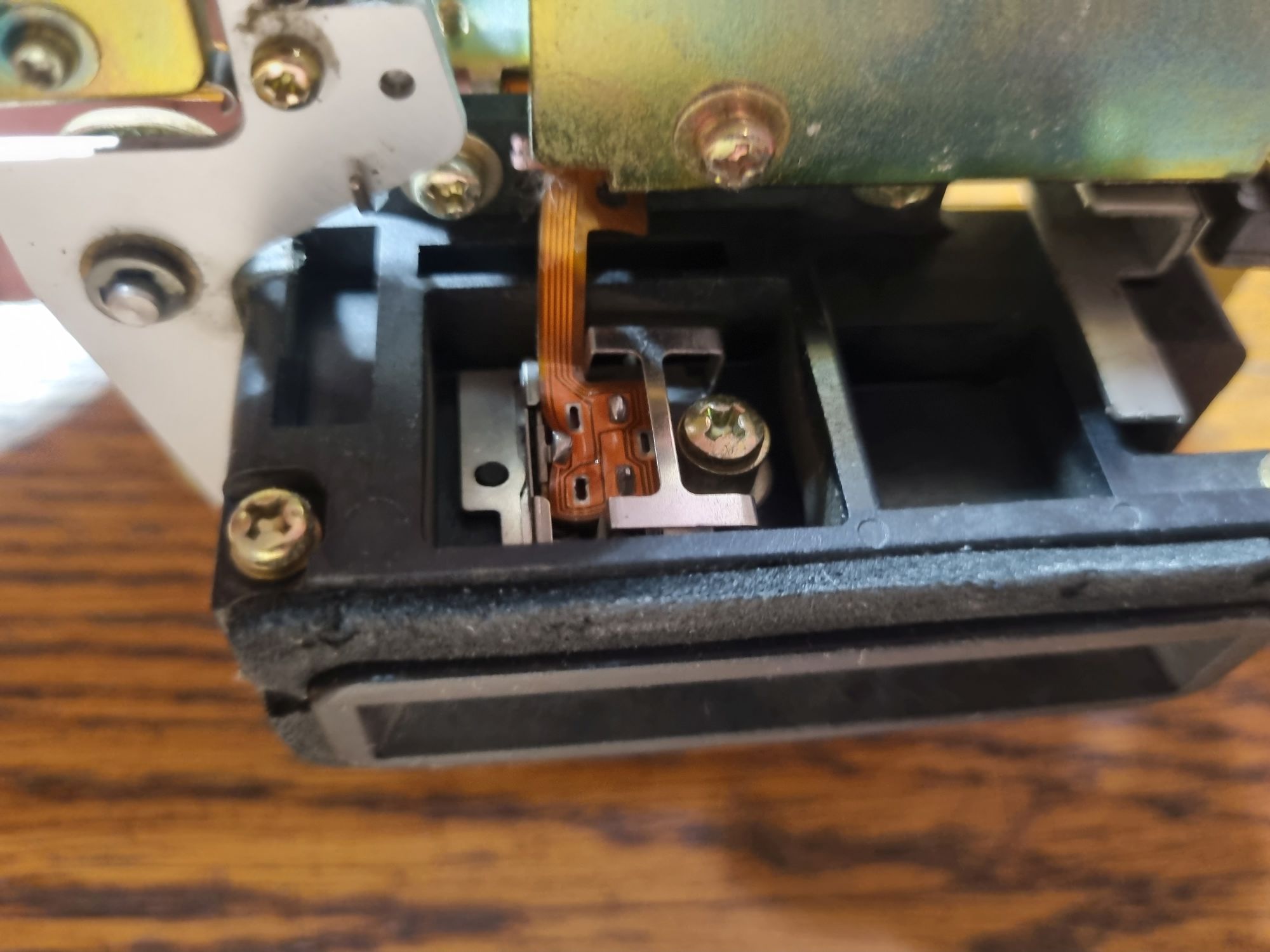
Unlike terminals, where the card slot is not protected by anything, everything here is much more interesting. If you look at this module from below, you can see the so-called pre-reading head. It does not read anything, but only detects that the inserted card contains a magnetic stripe. This is necessary to protect the reader from vandals (it won’t work to push a business card, a simple plastic card, or any other object of similar size into it) and inattentive users (a card inserted on the wrong side, due to the presence of raised letters on it, can get stuck or scratch the rubber rollers) .
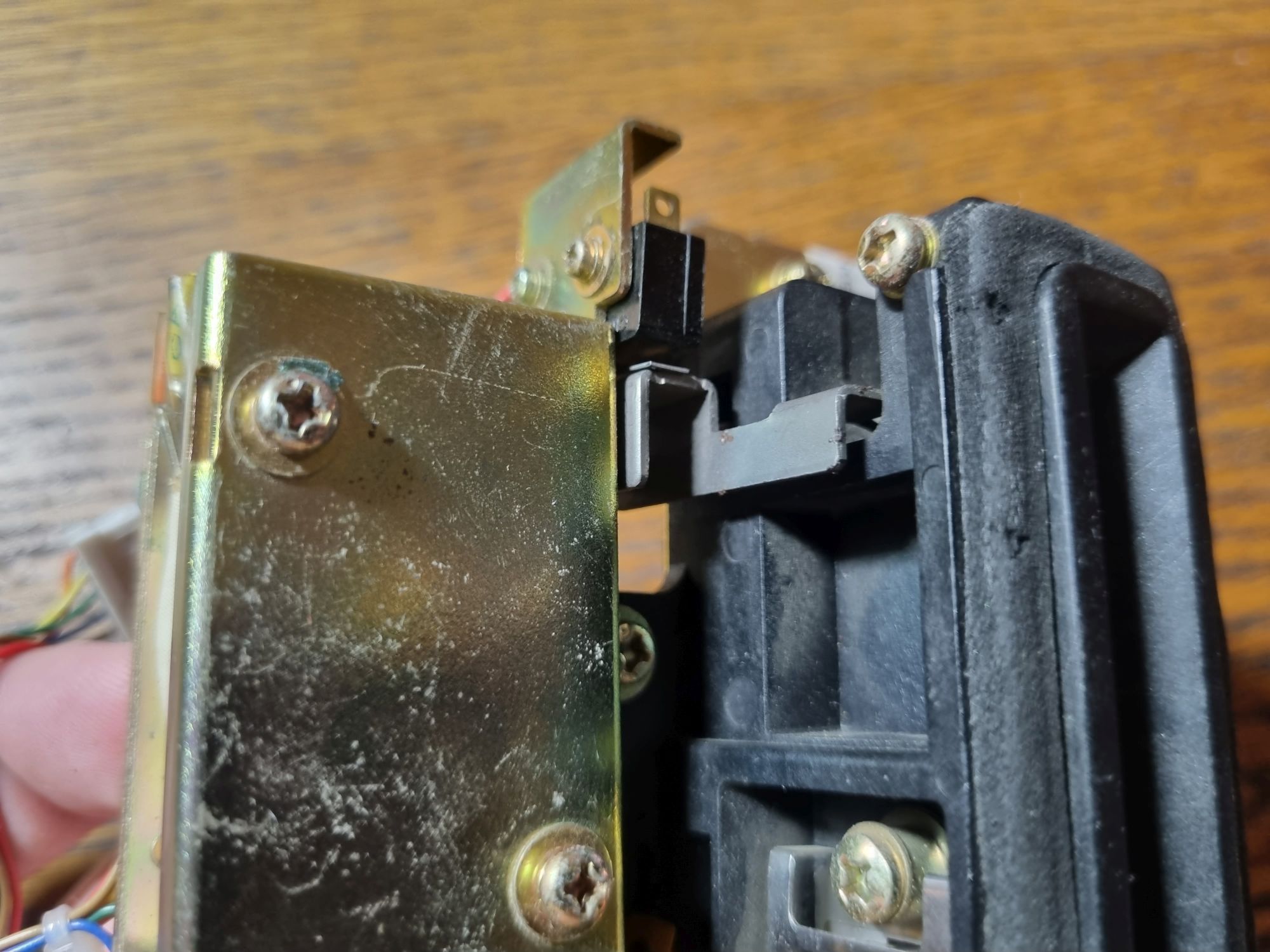
And here is a limit switch that is triggered when a card is inserted. It is to this that one of the inputs of the device is connected (in parallel with the card reader).

If the limit switch is triggered and the head sees the strip, the electromagnet opens the shutter, allowing the card to be pushed further. It is this moment that is controlled by the anti-skimmer. As you know, the most dangerous moment for a card happens when it is inserted. It is then that you need to muffle the potentially installed skimmer. In normal mode, the coil emits medium-power noise (to potentially prevent reading before the sensor is triggered, and also to prevent the skimmer from transmitting data over the radio channel, if there is one). When a card is inserted, the limit switch closes and the interference turns on at full power, preventing an outside device from reading the card data. Since the head in the skimmer is not shielded like in an ATM or terminal, the output signal is easily clogged with noise. When the limit switch is released, the interference power drops to a minimum: the card is inside, now the most important thing is not to interfere with its reading. Activity is also monitored by card reader consumption. A drive motor and electromagnets (curtains, swallowing mechanism, smart card reader drive) are installed inside it, which is why the start of its operation leads to a clearly visible surge of current.
There is also a relay installed inside the unit that allows you to turn off the power to the card reader in an emergency. When the capacitive sensor is triggered, the device understands that there is something foreign near the reader and can block work with cards if this is specified in its settings. These response thresholds are determined in the same control software.
❯ Something like that
Despite its effectiveness against very simple skimmers, very often this thing created a lot of problems.
The skimmers themselves quickly adapted to such devices – their creators learned to both compensate for interference and save dumps to the built-in memory. But for those who service ATMs, these devices have sucked a lot of blood. The coil caused such powerful interference that the magnetic head of the reader believed that the card was always there (moreover, the instructions for installing the device on some ATM models directly stated to disconnect its connector from the board), which is why the reader was triggered essentially only by the limit switch, which led to its damage from incorrectly or simply crookedly inserted cards. In addition, installing sensors on the receiving slot required special care: if, when closing the door (on some ATM models that had such a design), the card reader is not aligned with the slot on the door, then the card after insertion will no longer be able to come out on its own. Fortunately, with the spread of contactless and chip cards, the theft of magnetic stripe dumps gradually disappeared, causing the relevance of such devices to drop almost to zero.
So it goes.
You might also want to read this:
News, product reviews and competitions from the Timeweb.Cloud team – in our Telegram channel ↩