Webinar on Quest Change Auditor – Information Security Event Auditing Solution
Several years ago, when we started implementing Change Auditor in one bank, we noticed a huge array of PowerShell scripts that performed exactly the same audit task, but with a makeshift method. A lot of time has passed since then, the customer still uses Change Auditor and remembers the support of all those scripts as a bad dream. That dream could also become a nightmare if the person who served the scripts in one person would take and quit, in a hurry forgetting to pass on secret knowledge. We heard from colleagues that such cases happened in some places and that this then caused considerable chaos in the work of the information security department. In this article, we will highlight the main benefits of Change Auditor and announce a webinar on July 29 on this audit automation tool. All the details are under the cut.
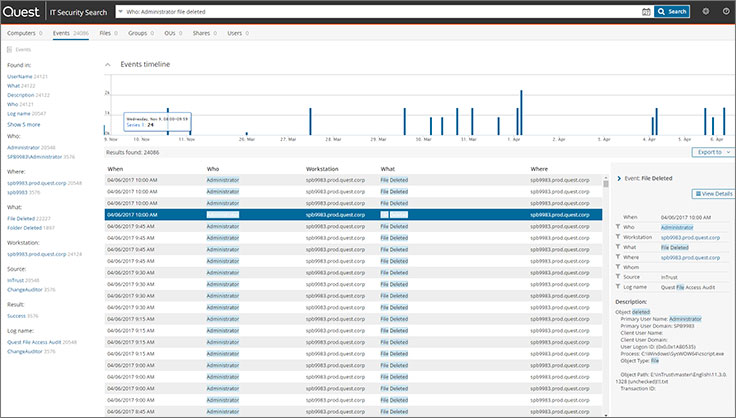
The screenshot above shows the IT Security Search web interface with a google-like search bar, in which it is convenient to sort events from Change Auditor and customize views.
Change Auditor is a powerful tool for auditing changes to Microsoft infrastructure, disk arrays and VMware. Auditing supported: AD, Azure AD, SQL Server, Exchange, Exchange Online, Sharepoint, Sharepoint Online, Windows File Server, OneDrive for Business, Skype for Business, VMware, NetApp, EMC, FluidFS. There are pre-installed reports for compliance with GDPR, SOX, PCI, HIPAA, FISMA, GLBA standards.
Metrics are collected from Windows servers in an agent-based way, which allows you to perform auditing using deep integration into calls inside AD and, as the vendor himself writes, this method detects changes even in deeply nested groups and introduces less load than when writing, reading and retrieving logs (this is how competing solutions work). You can check it at high load. As a consequence of this low-level integration, in Quest Change Auditor, you can veto certain changes for certain objects, even for Enterprise Admin users. Ie protect against malicious AD administrators.
Change Auditor normalizes all changes to 5W – Who, What, Where, When, Workstation (Who, What, Where, When and on which workstation). This format allows you to unify events received from different sources.
On June 2, 2020, a new version of Change Auditor was released – 7.1. The following key improvements have appeared in it:
- identification of Pass-the-Ticket threats (identification of Kerberos Tickets with expiration dates exceeding the domain policy, which may indicate a potential Golden Ticket attack);
- audit of successful and unsuccessful NTLM authentication (you can determine the NTLM version, and notify about applications that use v1);
- audit of successful and unsuccessful Kerberos authentication;
- Deploying agents for auditing in a neighboring AD forest.
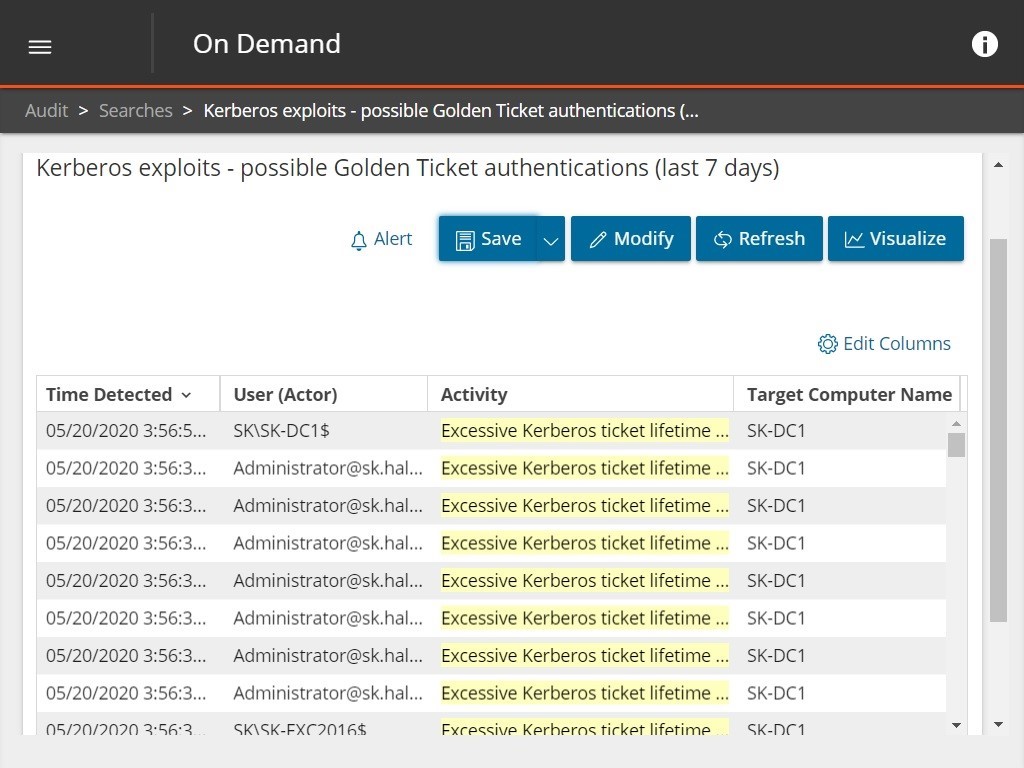
The screenshot shows an identified threat with a long Kerberos Ticket validity period.
Together with Quest’s other product, On Demand Audit, you can audit hybrid environments from a single interface and track logins to AD, Azure AD, and changes to Office 365.
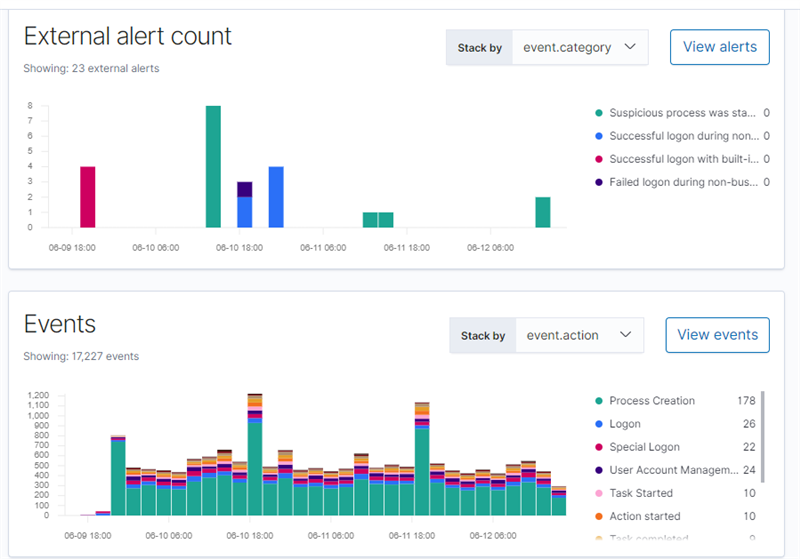
Another advantage of Change Auditor is the ability to integrate with a SIEM system directly or through another Quest product – InTrust. If you configure such integration, you can perform automated actions to suppress the attack through InTrust, and in the same Elastic Stack you can configure views and give colleagues access to view historical data.
To learn more about Change Auditor, we invite you to attend the webinar that will take place on July 29 at 11:00 Moscow time. After the webinar, you can ask your questions.
More articles about Quest security solutions:
Who did it? We automate information security audit
Tracking the life cycle of users without pliers and tape
What useful things can be extracted from the logs of a Windows workstation
You can leave a request for a consultation, a distribution kit or a pilot project through feedback form on our website. There are also descriptions of the proposed solutions.