Secret information? Use 2FA for VPS / VDS

The frequently asked question is how to reliably protect your VPS / dedicated server from hacking? So I decided to write a tutorial on how to implement two-factor authentication.
2FA is the second level of data protection, thanks to which you can access your account only after confirming your identity. Now, even if an attacker knows the username and password, thanks to two-factor authentication, he will not be able to access your server.
The presence of two-factor authentication reduces the likelihood of attackers accessing the account to almost zero, guaranteeing the safety of user data.
If you are still convinced that by coming up with a complex password, you are guaranteed to protect your server from hacking, and all personal data from theft, you are deeply mistaken. Today, hackers use a huge number of methods to quickly brute force even the most complex passwords, therefore two-factor authentication is the most important security measure that should not be neglected.
We pick up the phone and configure the authenticator application. This is easy enough. Different programs can be used, but I recommend Twilio Authy 2-Factor Authentication.
You can download it at this link: https://play.google.com/store/apps/details?id=com.authy.authy&hl=ru
Official site of the program: authy.com
The advantage of Twilio Authy 2-Factor Authentication is the ability to work on multiple devices at the same time, even on a desktop or laptop. Google Authenticator doesn’t have this option. If you suddenly lose your smartphone, you will save all your data for accessing accounts.
Install the application from Google Play and launch it. The system will then ask you to enter the country code and phone number. Be sure to include the phone number to which you have access. Also, do not forget to enter your e-mail.
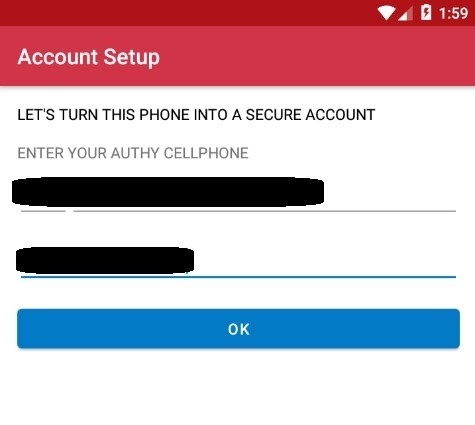
The next step is confirmation. Choose the method that is most convenient for you – receiving an SMS message or answering a call.
The authenticator package will need to be installed on the system. This is done as follows:
For Debian 9/10:root@alexhost:~# apt install libpam-google-authenticator - y
For CentOS first of all, you will need to connect the epel repository:root@alexhost:~# yum install epel-release
Only then can the package be installed:root@alexhost:~# yum install google-authenticator
At the next stage, we run root@alexhost:~# google-authenticator
The system will ask a question: Do you want authentication tokens to be time-based (y / n… We answer y, because this option is the most reliable.

To the question “Do you want me to update your” /root/.google_authenticator “file? (y / n) ” we answer y
To the question “Do you want to disallow multiple uses of the same authentication token? This restricts you to one login about every 30s, but it increases your chances to notice or even prevent man-in-the-middle attacks (y / n) ” we answer depending on how much you worry about security and are willing to sacrifice convenience for it.
The fact is that you can log in using an authenticator no more than once every 30 seconds. Not very convenient, but definitely safer.
Then we have one more question: “By default, a new token is generated every 30 seconds by the mobile app. In order to compensate for possible time-skew between the client and the server, we allow an extra token before and after the current time. This allows for a time skew of up to 30 seconds between authentication server and client. If you experience problems with poor time synchronization, you can increase the window from its default size of 3 permitted codes (one previous code, the current code, the next code) to 17 permitted codes (the 8 previous codes, the current code, and the 8 next codes). This will permit for a time skew of up to 4 minutes between client and server. Do you want to do so? (y / n) “ we answer y
Another question: “If the computer that you are logging into isn’t hardened against brute-force login attempts, you can enable rate-limiting for the authentication module. By default, this limits attackers to no more than 3 login attempts every 30s ”…
Again, see which is more important to you – convenience or safety. There is no single correct answer, it all depends on your preference. If you answer y, the system will allow a maximum of 3 login attempts within 30 seconds.

The next thing you will need to do is click on the + in the authenticator application and scan the suggested qr code in the terminal
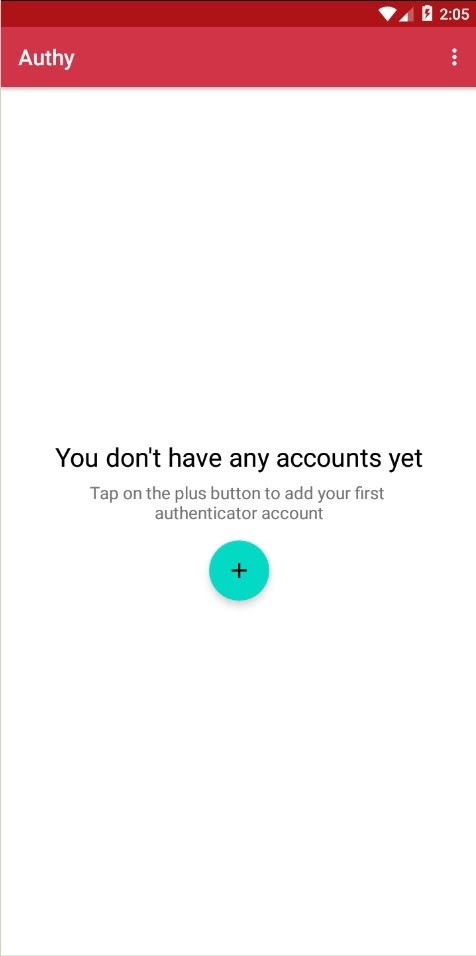
Then you need to set a security password for backups, which will consist of at least 6 characters. Of course, all accounts added to the app are saved in the cloud.
Save your account under any name you like

Attention! Remember to write down the emergency codes. In our case, these are:
Your emergency scratch codes are:
13455461
88816366
91315051
48752467
40022285
root@alexhost:~# nano /etc/pam.d/sshd
At the very end of the file, you will need to add “Auth required pam_google_authenticator.so”
Save the file Ctrl + O and then press Enter
Exit the editor by pressing simultaneously the Ctrl + X keys
By the way, you can use another text editor without any problems. You don’t have to use nano

Next thing to do:
“Root @ alexhost: ~ # nano / etc / ssh / sshd_config” replace “ChallengeResponseAuthentication no” on “ChallengeResponseAuthentication yes”
Be sure to add at the end of the file “AuthenticationMethods keyboard-interactive”
Press Ctrl + O and save the file, then Enter
Exit the editor Ctrl + X

At one of the last steps, you will need to restart the ssh serviceroot@alexhost:~# systemctl restart sshd
We connect. The system first asks for a password, then a two-factor key
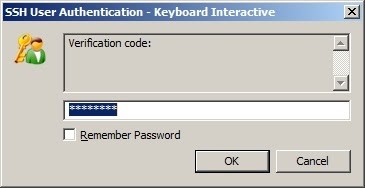
That’s it – congratulations, the setup is completed successfully!
A bit of advertising
1.5 GB RAM / 1 Core / 10GB SSD disk – 4 € / month or 11.88 € per year!
4GB RAM / 2 Core / 40GB SSD disk – 10 € / month or 60 € per year!
8GB RAM / 4 Cores / 80GB SSD disk – from 16 € / month or 144 € per year!
HERE – AlexHost.com