case of the Information Technology Center
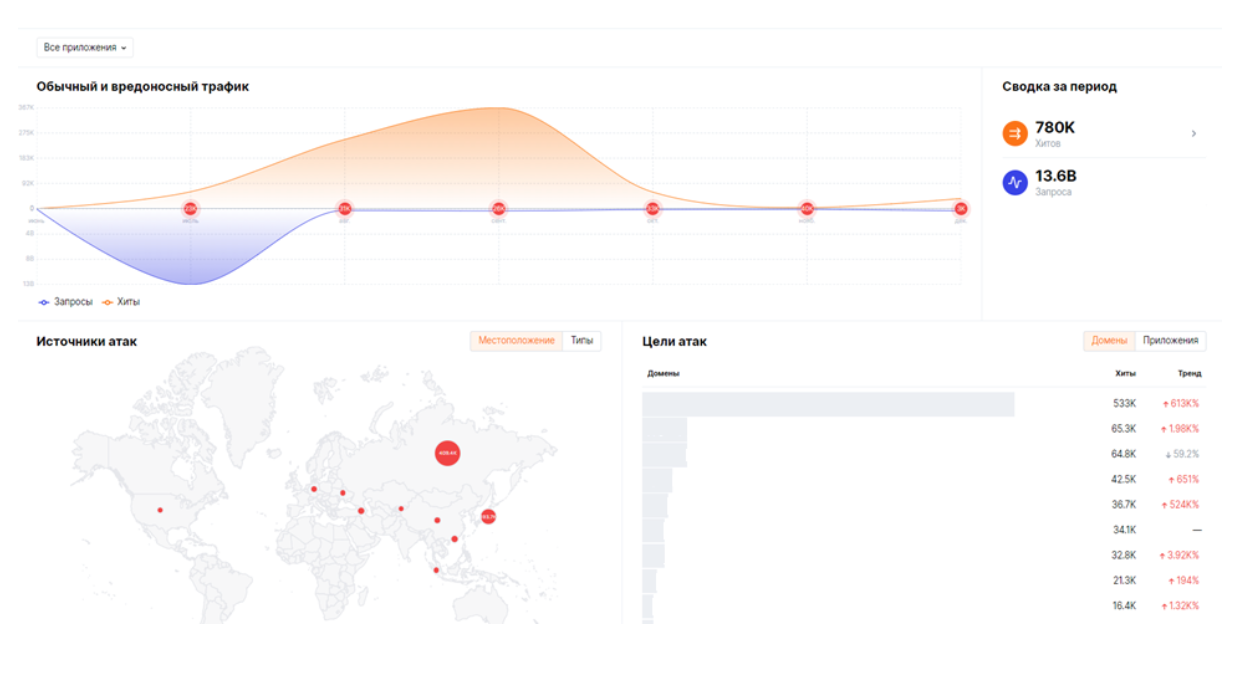
2022 turned out to be an extremely busy year in terms of the number and effort of computer attacks on Russian state resources. The information infrastructure of the Republic of Tatarstan, which faced new challenges, was no exception. The pressure on it in the form of distributed DDoS attacks and attempts to exploit vulnerabilities has increased tenfold compared to 2021. DDoS accounted for 20% of the total volume of recorded attacks on resources. The Information Technology Center of Tatarstan tells that it was necessary to develop protection mechanisms on the fly, and about the protection methods that were used to ensure the sustainable functioning and availability of public services.

It is worth noting that until February 2022, the level of DDoS attacks we recorded was insignificant. The main types were network and transport layer attacks of the OSI model. This type of attack was well recognized and blocked by the current DDoS protection system.
With the beginning of CBO, the types of DDoS attacks moved to the “new” level of the OSI model. The graph shows the distribution by type of protocols of a typical attack in 2022. It can be seen that the vast majority of requests are for https:
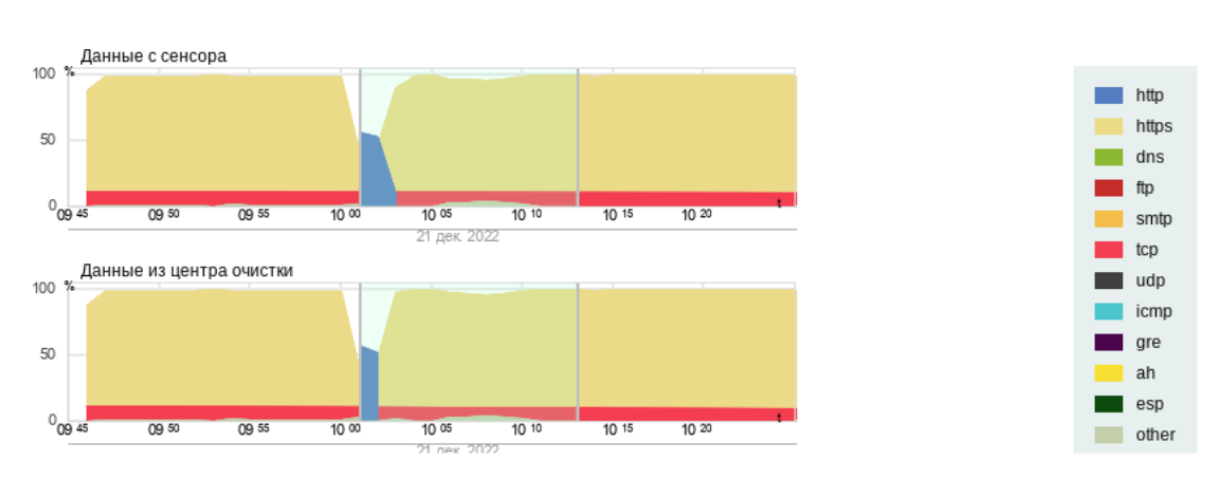
There were L7-level attacks before, but it was in 2022 that their volume increased so much that many were not ready for this. Consider what we did in similar conditions.
Filtering by GEO IP
Of the effective methods that can radically reduce the load on web applications and security systems, is filtering by GEO IP. We allow requests to resources only from Russia and countries from which attacks are not observed.
Filtering by GEO IP is possible both at the WAF level and at the level of the existing DDoS protection system. It is wiser to use filtering systems to protect against DDoS attacks. It allows you to remove up to 90% of illegitimate requests that are not recognized by security systems as an attack.
The issue of filtering by GEO IP has several nuances:
1. GEO IP bases are not always accurate.
2. It is necessary to periodically add to the white lists the external IP addresses of those who definitely need to connect from abroad.
3. Citizens wishing to receive services from abroad experience difficulties.
4. GEO IP is not a silver bullet. Attacks will continue from Russian IP addresses.
Blacklists
So, filtering by GEO IP allows you to reduce the load at times when the protected resource is under attack. Attacks can last from a few hours to a couple of weeks. Prior to February 2022, attacks rarely lasted more than an hour.
Since the load is still high, we are looking for additional ways to reduce the load. They come to help proxy server lists, which can be automatically downloaded from various resources. In this case, we used github. This made it possible to reduce the load by another 20-30% of detected attacks.
Unfortunately, we have not found a single open source of feeds containing information about attacking hosts. In the early months of attacks, this source would be very useful to many small companies experiencing difficulties with DDoS attacks.
Working with hosters
Next, we will consider additional methods that can also be useful when repelling DDoS attacks.
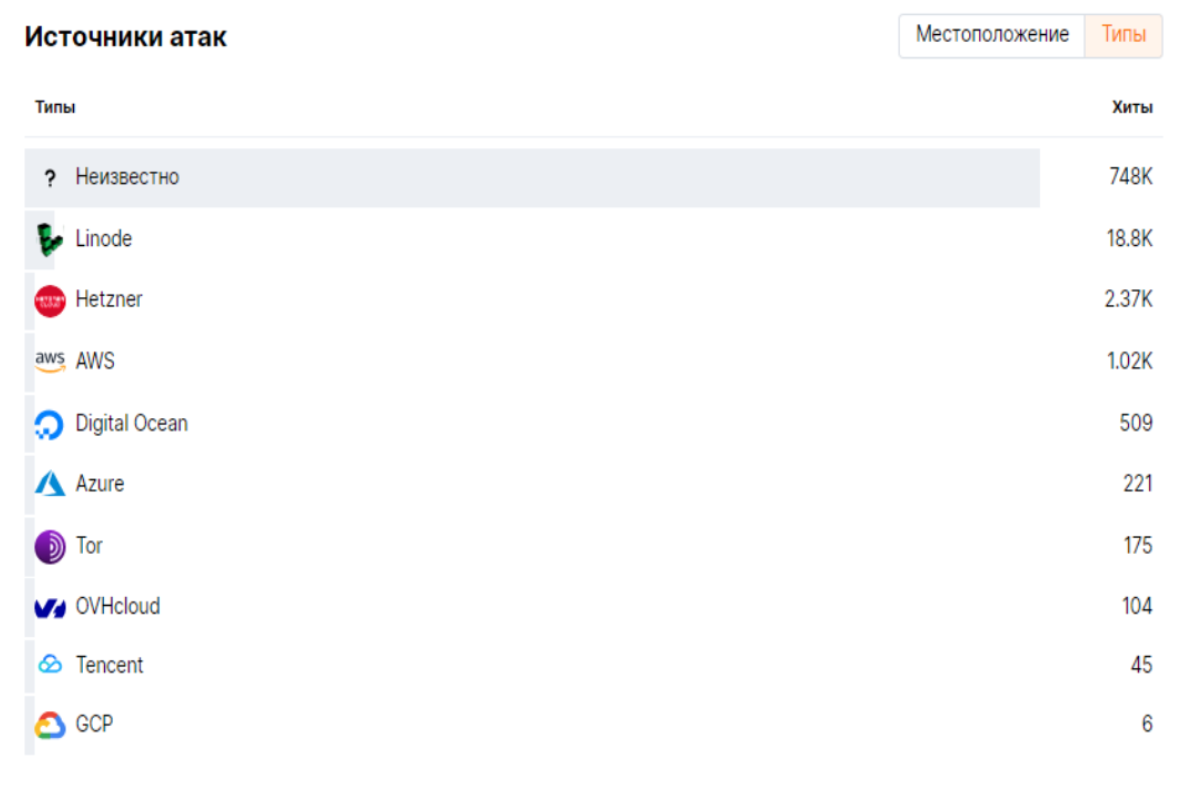
A large number of requests during the attacks came from IP addresses of hosting providers. The figure below shows the distribution of attack sources by hosting, which we recorded in WAF.
And if we did not even try to communicate with foreign hosting providers, then communication with Russian hosting we tried to line up despite the lack of time. And it has borne little fruit.
DDoS protection at the WAF level
Last but not least are DDoS protection tools. at WAF level. In addition to requests that have clear signs of an attack, there are a large number of requests that are indistinguishable from legitimate ones from the point of view of WAF.
The functionality of the WAFs we use allows us to carry out a statistical analysis of requests, on the basis of which the WAF makes a decision to block the request. The conditions for triggering a particular trigger must be configured, taking into account the specifics of the protected application. The task of the analyst is to find the optimal trigger thresholds.
The task of collecting access statistics is laborious in terms of computing resources. Therefore, it can be used when the attack power is insignificant or the traffic has been previously cleared at the level of firewalls and DDoS protection tools.
Outcome
Methods for blocking DDoS attacks are not limited to those listed in this article. Rather, we cited those methods that, under certain conditions, seemed to us the least labor-intensive and most effective.
Using the methods described above, at the peak of massive attacks, we managed to filter out over 12 billion illegitimate requests and block up to 15 thousand unique IP addressesfrom which the attacks were observed. This made it possible to maintain the availability and ensure the stable functioning of web resources.
What methods do you use? Write in the comments.