Audit in 60 minutes – free of charge, we check the resilience of employees to phishing attacks through Sophos Phish Threat

Surely many of you were interested in the question: “How many of my colleagues are not aware of phishing attacks?” To clarify this question, you can be a little confused and take up local utilities, but it is much more efficient to use a ready-made solution.
Action plan:
- request a test version of Sophos Phish Threat;
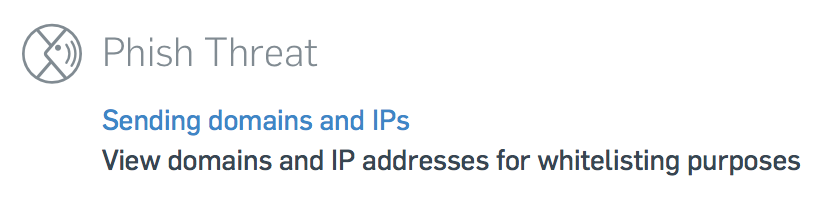
- add Sophos IP addresses to the white list;
- choose and edit the template under our realities;
- do the newsletter;
- look at the statistics;
- We talk with users and management.
A more detailed description can be found under the cut.
At the end of the article – a bonus for those who read to the end;). Employee Decision Card – print and distribute to all employees.
Recently, phishing attacks have increased dramatically, as attackers continue to improve tactics and share successful types of attacks. In particular, they take advantage of the darknet malware to increase the effectiveness and volume of attacks. In fact, a huge number of organizations are currently reporting at least daily phishing attacks. Here we look at the evolution of phishing in recent years, how it works and how it looks. And since cybercriminals continue to hunt employees with their technology, we will argue for the importance of multi-level protection against phishing attacks: a combination of advanced security technologies with employees aware of phishing.
More than annoying spam
Traditionally, phishing has been associated with cybercrime online banking: scammers send an email, luring you to a website that is a visual clone of your bank login page, where you enter your credentials into a fake form and put them directly into the hands of criminals. But phishing covers much more than just fake banking sites and imaginary links. Phishing is big business. In recent years, the amount of phishing attacks supported by “dark” web services, such as free phishing kits and phishing as a service, has increased dramatically. Even an attacker with a small technical background, it is becoming easier to use advanced malware. As a result, phishing attacks have become a regular part of everyday life.
The main driving force behind phishing attacks is financial gain. A Verizon 2018 data breach research report showed that:
- 59% of attacks are caused by financial gain. It also includes collecting credentials for resale on the darknet, infecting systems with ransomware, or impersonating managers to convince employees to transfer funds or transfer valuable data.
- 38% of attacks are aimed at obtaining unauthorized access to the system. Examples include obtaining company access to steal data or gain control over systems.
Currently, most phishing attacks are carried out by organized crime. This has led to more effective methods of spreading attacks using phishing services, ready-made phishing kits and new types of attacks that target more valuable assets using social engineering.
Increasing employee awareness of phishing using Sophos Phish Threat
With the help of Sophos Phish Threat, you can conduct an audit – emulate a phishing attack and check how employees are exposed to this type of threat. To do this, request the Trial of the product and enter Sophos Central, the Phish Threat section.
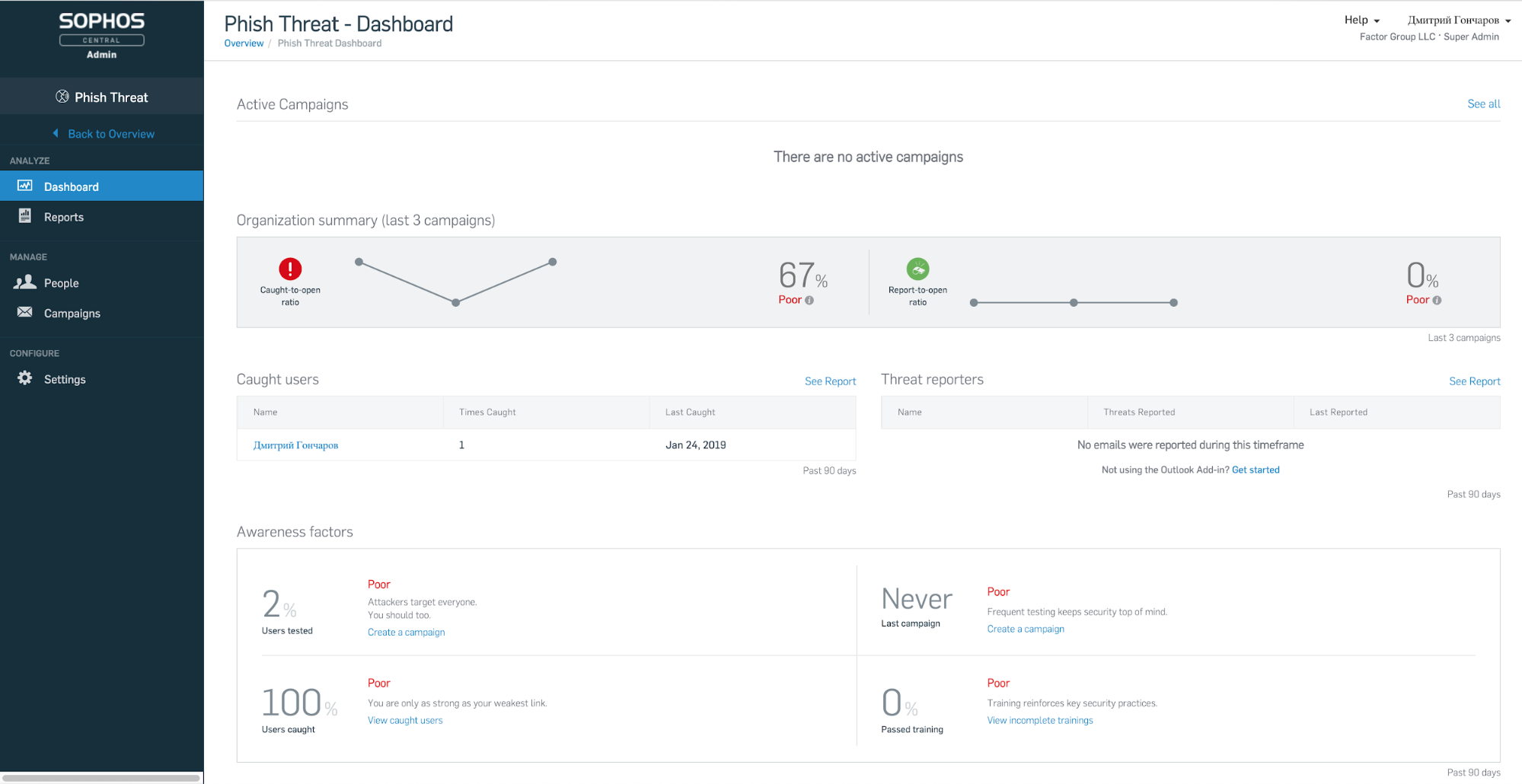
The Dashboard tab displays summary information on the last three phishing attacks in our example. You can see how successfully the phishing campaign ended, which employees were at risk.
On the Settings tab, we look at the IP addresses from which the distribution will take place.
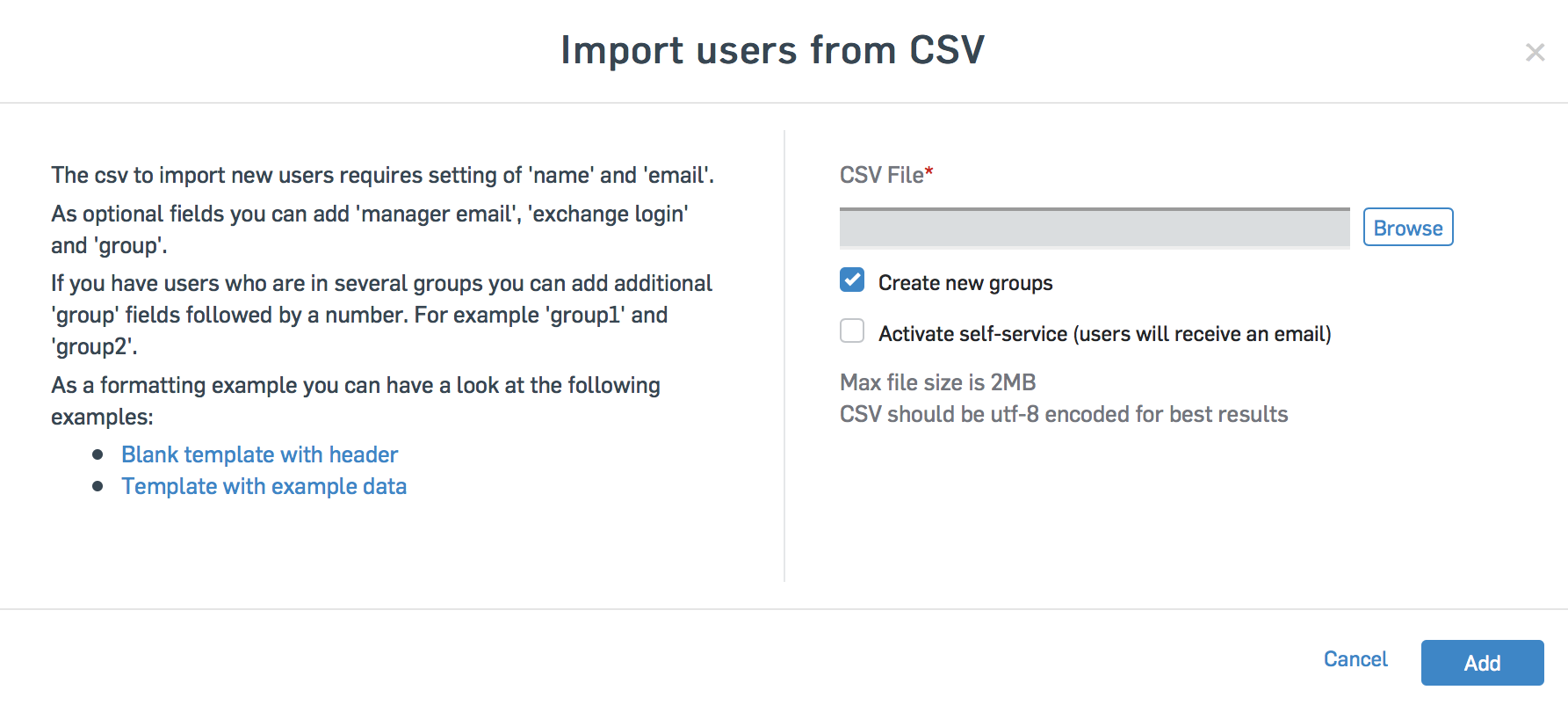
On the People tab, we add employee email addresses. You can do this in several ways: import from a CSV file, add manually, synchronize with Active Directory, synchronize with Azure AD.
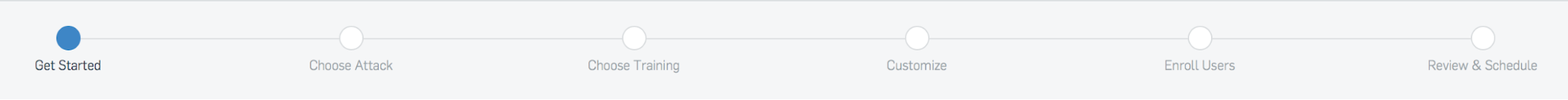
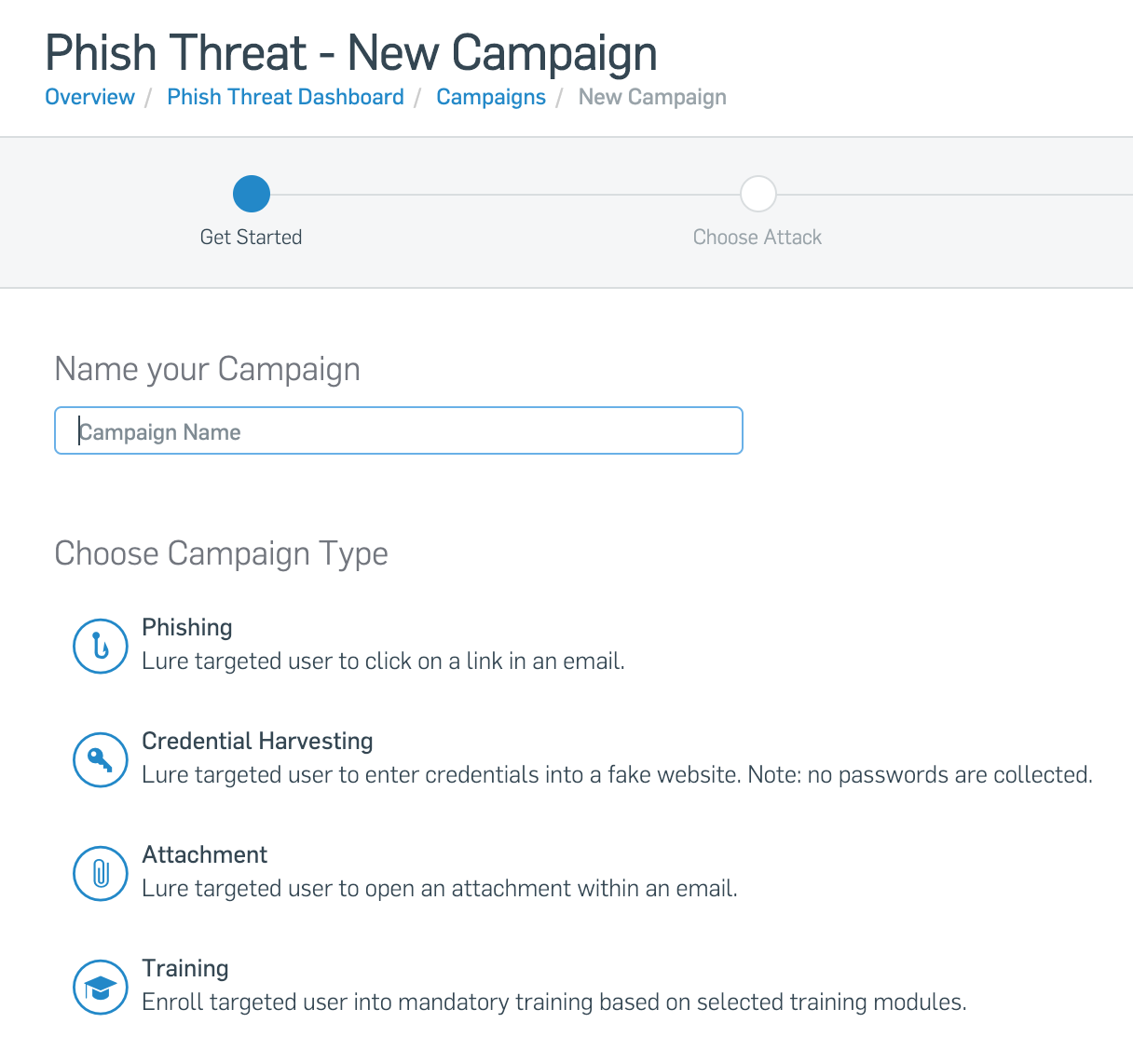
Now let's move on to creating a phishing mailing – on the Campaigns tab. The process is divided into stages, from the top you can see their passage.
At the first stage it is necessary to choose the type of distribution. This may be the usual phishing, which is aimed at identifying the transition on phishing links. Another type of phishing is collecting credentials. It aims to identify the possibility of collecting credentials from a phishing site. It should be noted that the entered data is not saved. The third type is phishing with attachments. It detects the user opening an attachment in an e-mail.
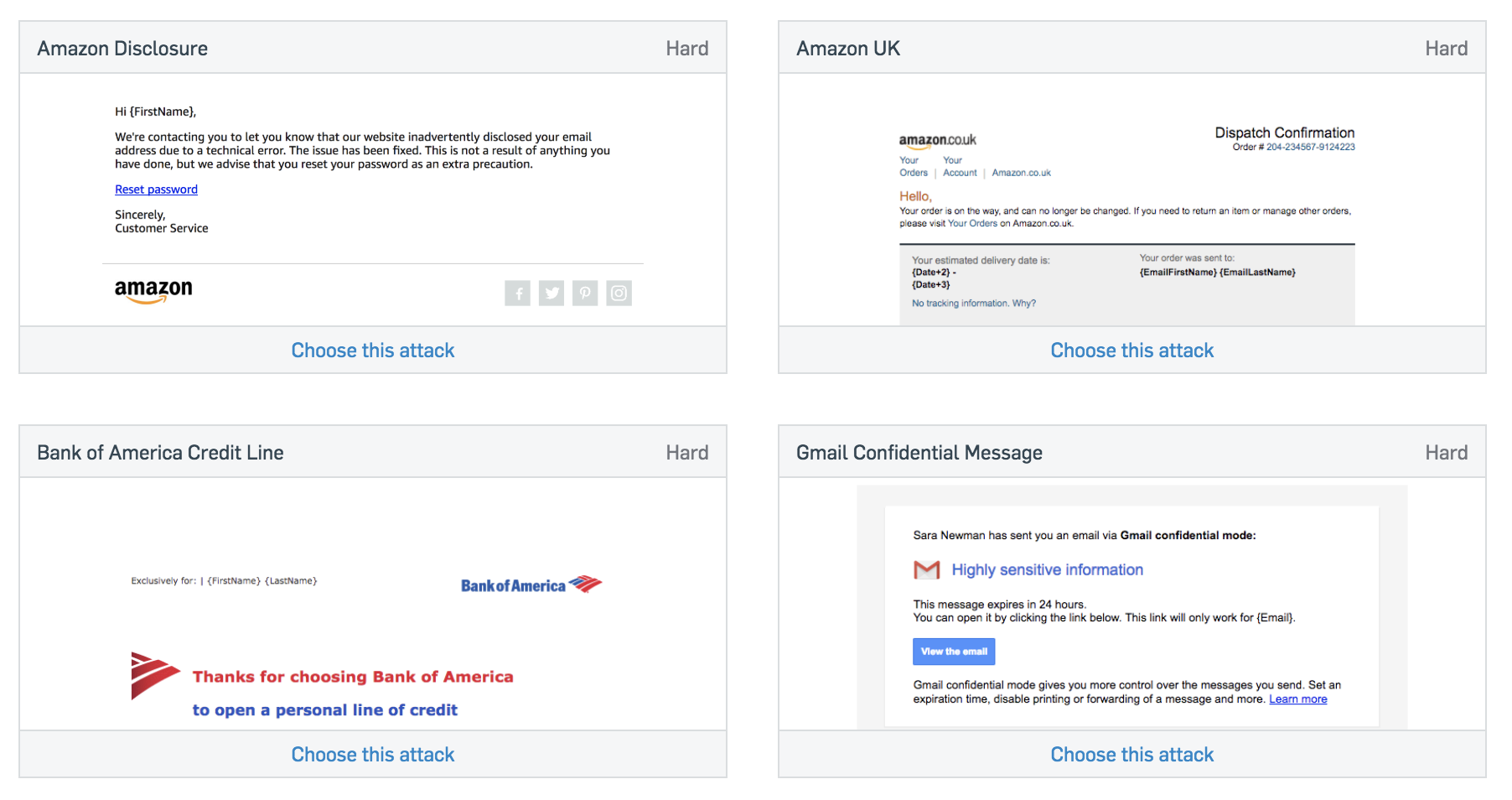
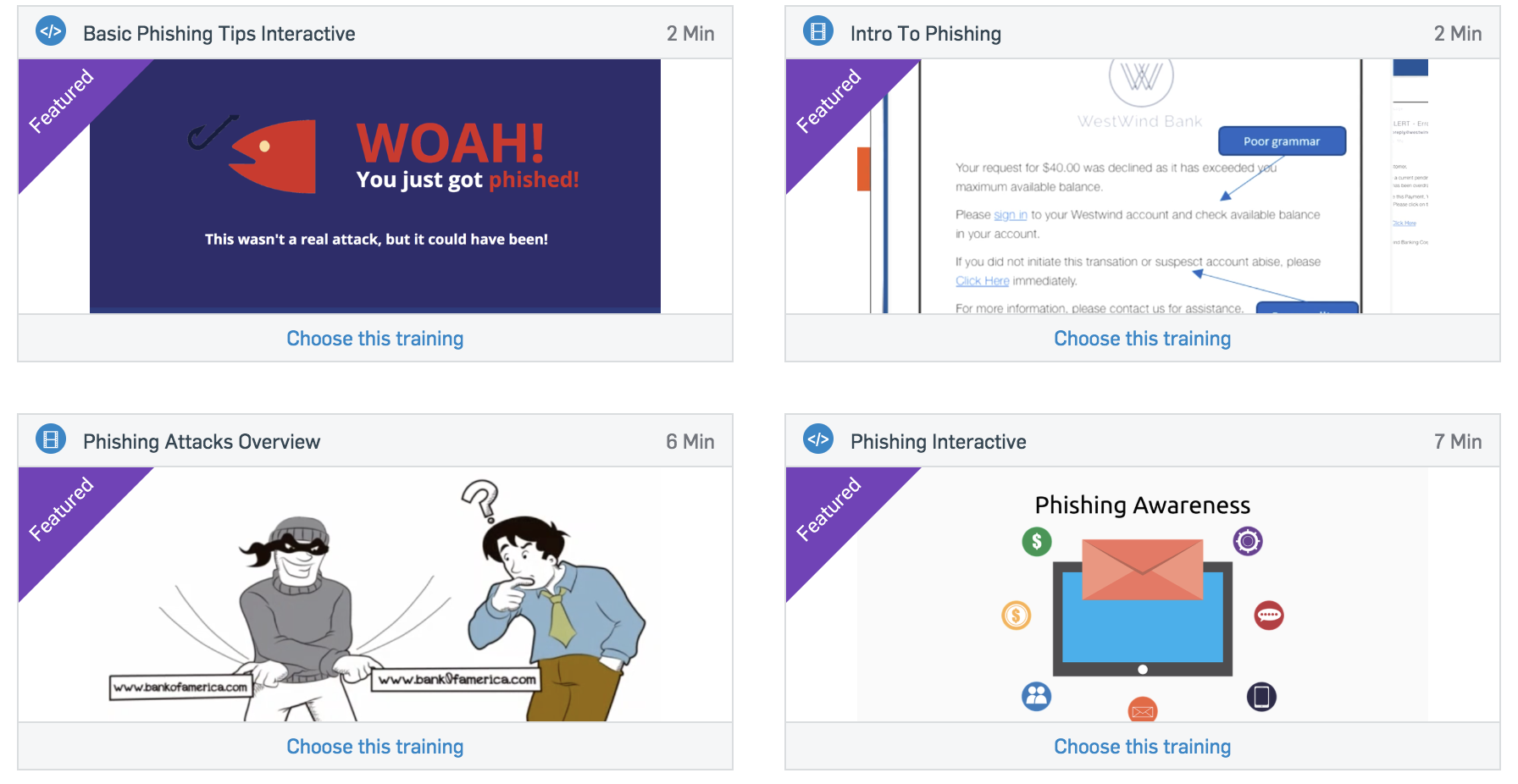
Once we have decided on the type of phishing attack, choose a phishing email template. In this regard, Sophos has a wide variety to choose from. SophosLabs analysts track the latest trends in real-world attacks and regularly update templates.
Then you need to choose a training for the user, which will be demonstrated to him as a training material. Currently, trainings are not available in Russian, so you can use them as a basis for creating your own seminars within the company. You can also set the URL to your internal training – for example, in the internal knowledge base.
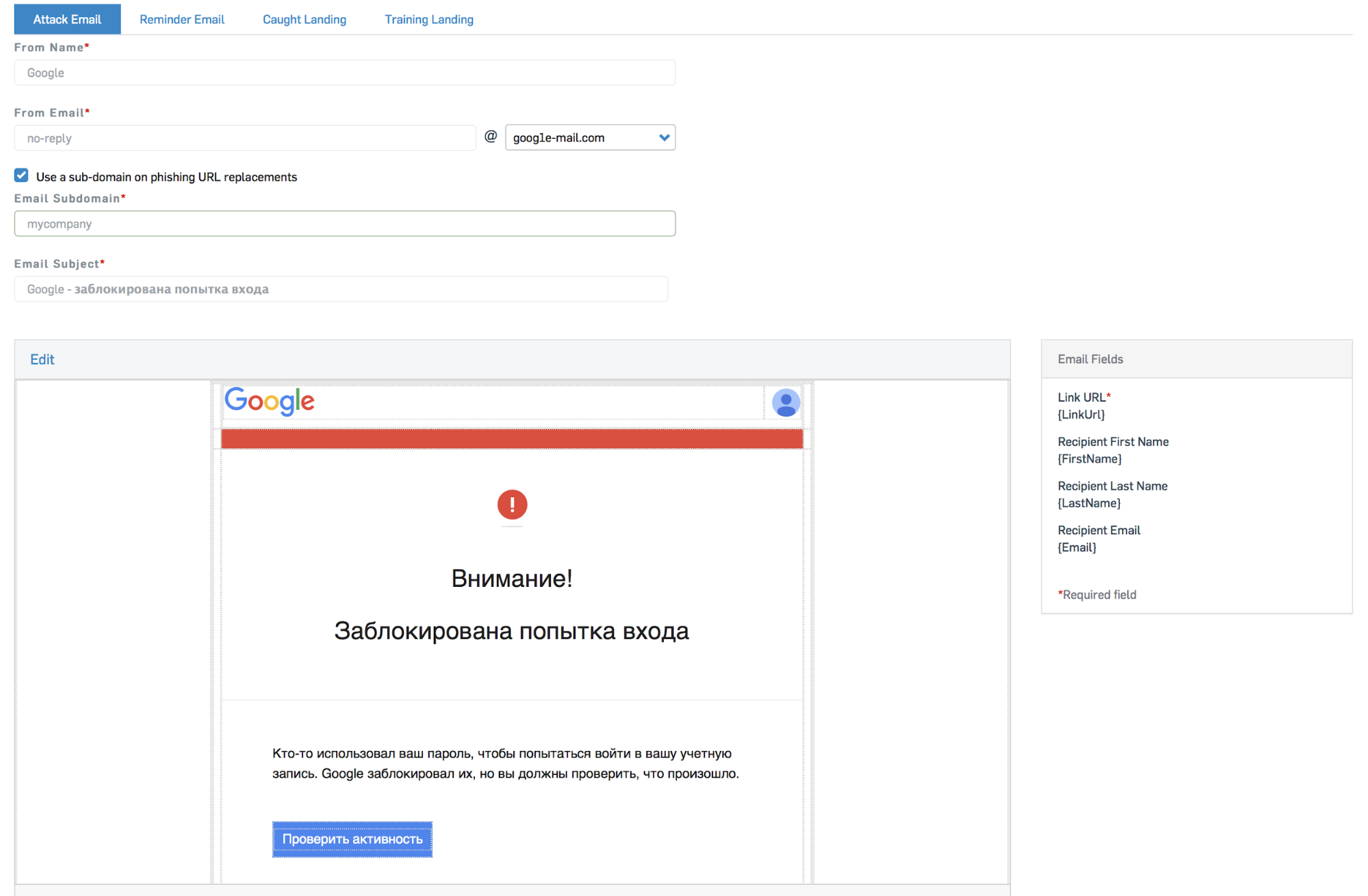
After this we customize our newsletter. Register the Name and Email address that will be specified as the sender, edit the letter template – we can insert the necessary pictures and write the text in any language.
We select users / groups – here we can select the relevant department for which we prepared the letter template.
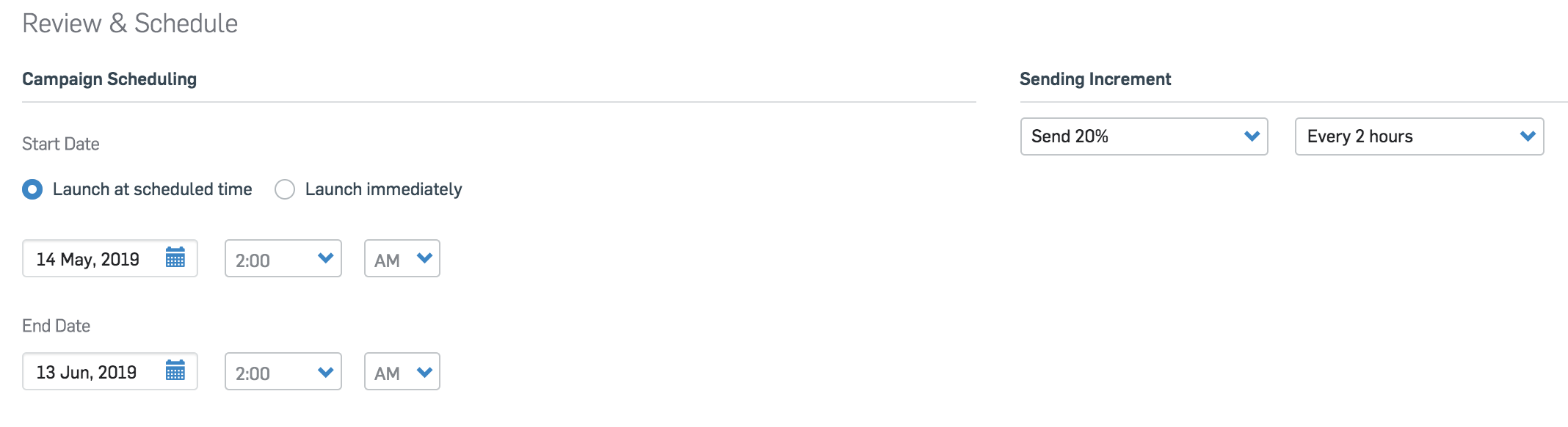
Specify the time interval in which the phishing mailing will be carried out. You can send letters to all users at the same time, or you can make it more cunning – send gradually, for example, 20% every 2 hours (total – 5 hours for the entire newsletter). This is useful for a large number of users and that not all users receive the same email at the same time.
Push the treasured button Done and go to drink coffee …
Audit analysis
After the phishing mailing, we’ll proceed to the report.
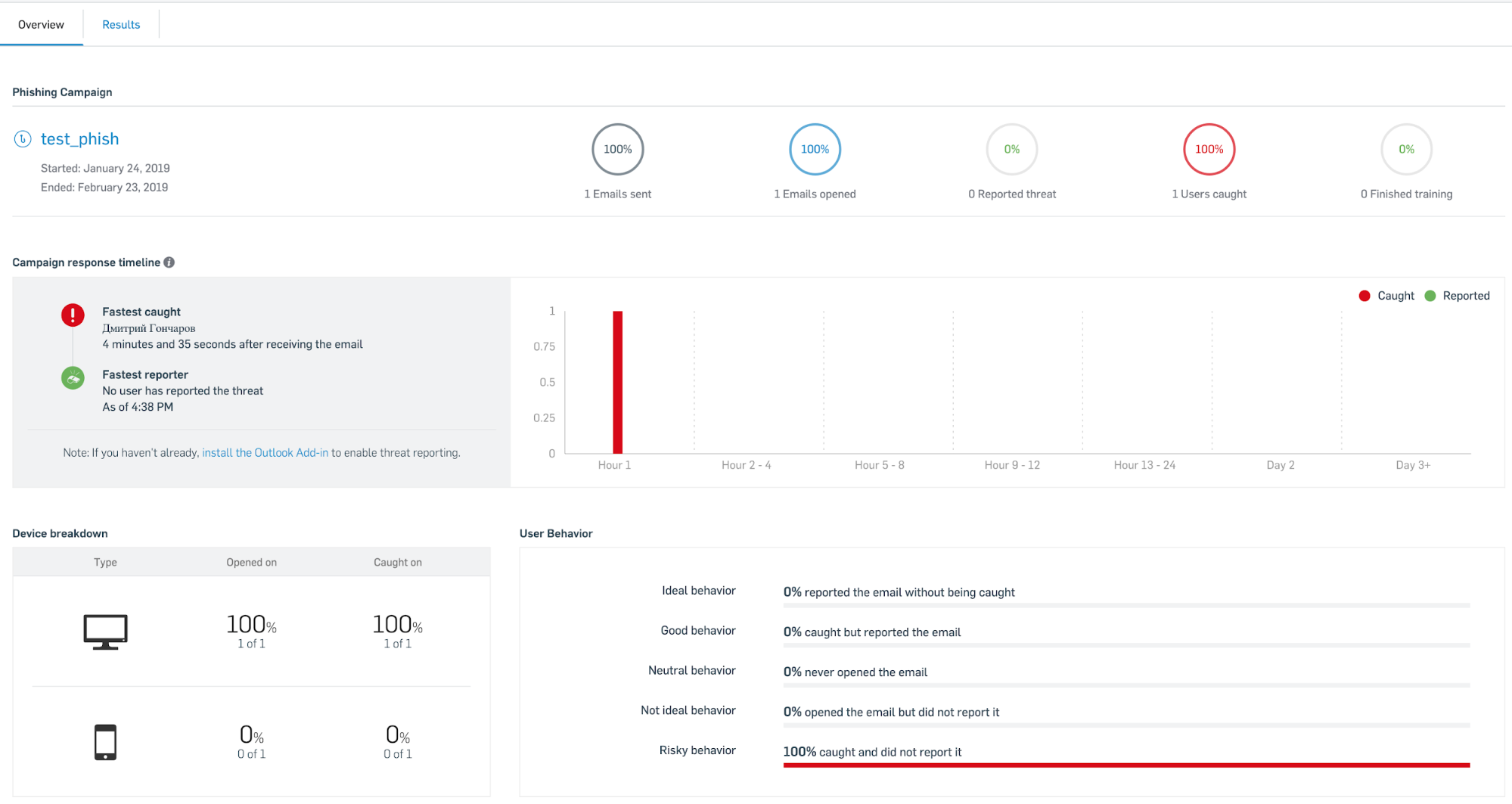
The report displays the types of devices that have been attacked, the number of messages sent, open messages, the percentage of users who have been attacked. You can also see which users are the fastest to open a phishing email.
Thus, we considered a tool for phishing mailing in a company like Sophos Phish Threat, which is quite flexible in its settings, and, among other things, contains training sessions for the prevention of real phishing attacks in the future.
The end user decides whether to open the attachment or follow the link. To help the average user, we have prepared two documents in Russian:
phishing detection flowchart;
phishing checklist — print and hang on the wall.

To keep users in good shape, such training should be carried out on a regular basis. If you are interested in the decision, you can contact us – Factor Group, Sophos distributor. It is enough to write in free form at sophos@fgts.ru.
Thanks for the help in writing the article thanks popov-as